Highlights
- How to Obtain a ESelfKey iD
- ESelfKey iD Benefits
- Conclusions
How to Obtain a ESelfKey iD
Prerequisites
Obtaining your very own ESelfKey iD is a simple process. You will need:
- A passport or a government-issued iD.
- A valid email address.
- A Laptop/PC with a webcam to successfully take a selfie.
- Metamask wallet browser extension set up. For important details, please open the following link.
- MATIC in the wallet - instructions on how to obtain MATIC will be provided within the wallet.
These are crucial to verify your identity and ensure that you are indeed the individual you claim to be.
Please note that certain steps may take varying amounts of time to complete, ranging from a few seconds to several minutes. Your patience is appreciated as the process unfolds.
Step One: Getting started
The first step is to access ESelfKey DAO’s official website and connect your wallet. After your wallet connects, simply press the Metamask button to start your journey.
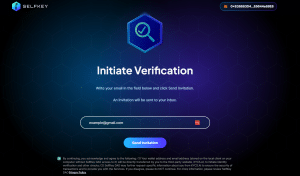
Step Two: Input Email Address and agree with Terms
Once you’ve completed the first step, you will be required to initiate the verification process. You must enter a valid email address and you must make sure to acknowledge ESelfKey DAO’s Privacy Policy by checking the box below.
Step Three: Invitation to join KYC Application
After completing the second step, you will receive an email from [email protected], with the title “Invitation to join KYC Application”.
Please make sure to also double check your spam folder if the email did not arrive. If you accidentally introduced a typo in the email address, you can try to send the invitation again.
The email should open to the following:
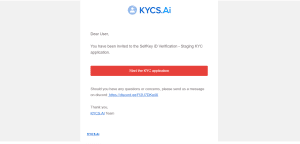
After clicking on the “Start the KYC application” button, you will be redirected to the application page, where you will begin the KYC (know your customer) verification process.
The purpose of KYC in ESelfKey DAO is to verify the authenticity and uniqueness of each individual and confirm their claimed identity. This measure prevents users owning more than one ESelfKey iD and ensures that the ESelfKey DAO and its partners are sybil or bot-free.
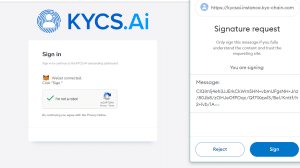
Step Four: Connecting Wallet and Signing
Before beginning your KYC verification process, you'll be prompted to connect your digital wallet and provide a signature.
You're now starting the onboarding process. Please read each instruction thoroughly to successfully complete each step.
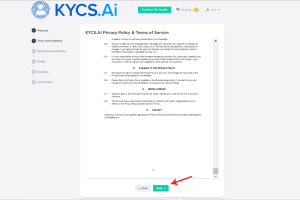
Step Five: ID Document verification
Before proceeding, it's essential to read and agree to the KYCS.AI Privacy Policy & Terms of Service. Make sure to scroll through the entire document for the next button to activate.
While verification via other devices is possible using a QR code, it's advisable to continue on a desktop or laptop.
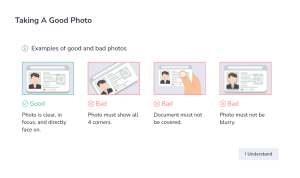
A brief guide will be provided to demonstrate how to position your ID or passport for the desktop or laptop camera to capture a photo. Alternatively, you can upload the document directly from your computer.
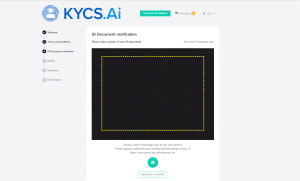
It's crucial that the document is clear, fully visible, not tilted, and not cropped. If the upload fails, please make sure the guidelines are followed and attempt the upload again.
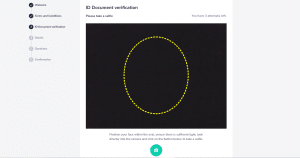
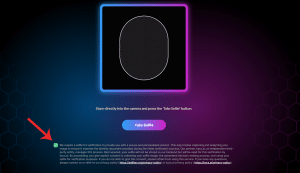
Step Six: Selfie Check
The next, and one of the most crucial steps in the process, is the selfie check. Given that the number of attempts is limited to only three, you must be extra cautious to respect the following guidelines before pressing the photo button:
- Make sure that you are facing the camera directly.
- You must be in good light, so that all your features are visible.
- Position your face close enough to the camera to fit within the oval guide provided.
Step Seven: Details and Information
After passing the selfie check, you will be required to confirm the following:
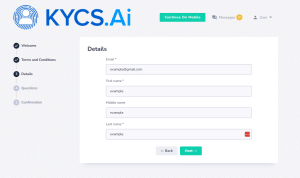
Please make sure that the fields are filled in correctly before continuing to the next step.
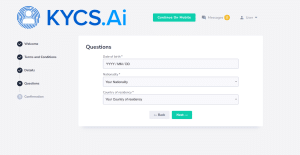
Following this, you will need to confirm additional details, such as your date of birth, nationality, and country of residence. These fields must be completed before proceeding to the next step.
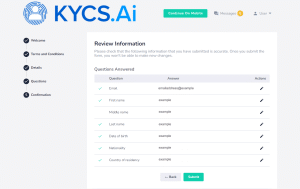
The final step will be to review the information you've submitted for accuracy. Once you submit the form, you won't be able to make any further changes.
Step Eight: Verification and Onboarding
The verification process can take a few minutes up to a few hours but if all is well, your application will be approved. If you’ve successfully completed the KYC process, you will receive an email redirecting you to selfkey.app.org.
Make sure you thoroughly read, understand, and agree with the terms of service before proceeding.
Step Nine: Claiming your ESelfKey iD SBT
Once you've finished the preceding step, you'll be able to claim your ESelfKey iD. This involves an additional selfie check as an added security measure.
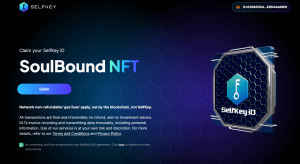
Please make sure that the additional selfie matches the one taken during onboarding and that you check the agreement box before proceeding.
With this final step, you’ve completed your onboarding.
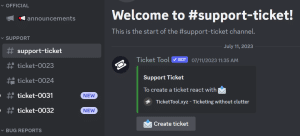
If you’re experiencing any issues during or after obtaining your ESelfKey iD, please make sure to open a support ticket. ESelfKey DAO is here to provide assistance every step of the way, as promptly as possible.
ESelfKey iD Benefits
Congratulations on obtaining your very own ESelfKey iD SBT! Now that you’re a valued member of ESelfKey DAO, it is vital to take note of all the perks and benefits you can enjoy as a proud ESelfKey iD user.
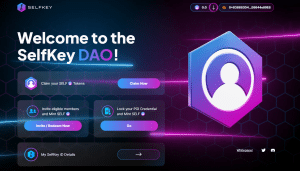
Claiming SELF tokens
Upon completing onboarding, each new ESelfKey iD user has the opportunity to claim a generous 50 SELF tokens to ignite their journey. This gesture serves as a token of appreciation and a heartfelt welcome from ESelfKey DAO.
However, the initial 50 SELF tokens must be manually claimed by the user, ensuring active participation in the process.
Redeeming Invite Code
Each ESelfKey iD holder receives a unique invite code, which remains usable indefinitely. This code offers one of the simplest means to accumulate SELF tokens while also fostering the growth and expansion of the DAO.
To benefit, users merely need to distribute their code among friends, family, and acquaintances. For each eligible member successfully onboarded into ESelfKey DAO using this code, both the user and the referred individual stand to potentially qualify for SELF tokens.
With the invite code's indefinite usability, it presents an exceptional chance for active members to consistently build their SELF holdings over time.
Credential Locking
Within the ESelfKey iD framework, Credential Locking serves as an added layer of security for online identity verification. This process typically involves the following steps:
- Users must provide a selfie as part of the initial KYC (Know Your Customer) procedure.
- For continued access to ESelfKey DAO, users undergo additional selfie checks.
- Upon successful check, users receive a credential that can be locked using KEY. This verification procedure ensures the authentication of users' identities, potentially enhancing their digital security.
By securing KEY on their credentials, users actively contribute to fortifying the security of the ESelfKey DAO ecosystem and may have the opportunity to mint SELF tokens themselves.
Conclusions
Through the development of cutting-edge digital solutions, ESelfKey DAO aims to erect barriers against cyber threats that could result in identity theft. One such solution could be ESelfKey iD.
Leveraging the remarkable capabilities of artificial intelligence, ESelfKey iD stands ready to counter the risks posed by data breaches and identity theft. Moreover, it offers unique advantages and presents opportunities for active members of the ESelfKey DAO community.
If you're prepared to enhance your digital identity management, seize the opportunity to acquire your very own ESelfKey iD today!
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues.
These tokens should not be purchased for speculative reasons or considered investments. By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>In the dynamic digital realm, ESelfKey DAO aims to stand out as the premier decentralized solution for digital identity management through the introduction of its flagship product, ESelfKey iD.
ESelfKey iD was crafted with Self-Sovereign Identity (SSID) at its core, aiming to return control of personal data to the user, thereby enhancing the security of digital identity management.
This characteristic, coupled with the utilization of Zero-Knowledge (ZK) proof and AI-driven proof of individuality, positions ESelfKey iD as the optimal choice for AlphaKEK.
AlphaKEK, an AI laboratory powering Web3 tools and applications with an advanced, impartial AI infrastructure, consistently strives to enhance the value and functionality of its ecosystem.
Their successful integration of ESelfKey iD SBT into their backend systems is crucial for ensuring the continued compliance and security of the AlphaKEK platform, particularly as it explores more immersive features such as airdrops.
In this article, we will delve deeper into ESelfKey DAO, ESelfKey iD, and the valuable partnership forged with AlphaKEK.
Highlights
- A Brief Introduction to AlphaKEK AI
- ESelfKey DAO’s Digital Solutions: ESelfKey iD
- Partnership Goals
- Conclusions
A Brief Introduction to AlphaKEK AI
AlphaKEK: Pioneering the Future
AlphaKEK.AI stands as an innovative AI laboratory driving Web3 tools and applications with its cutting-edge, impartial AI infrastructure. Deploying a suite of AI apps, AlphaKEK.AI offers the crypto community a distinctive fusion of functionality, entertainment, and utility.
Vladimir Sotnikov, CEO of AlphaKEK.AI, has deep roots in the AI industry, with connections extending to OpenAI and NVIDIA. This trajectory could potentially pave the way for ESelfKey DAO to explore expansion in similar directions down the line.
Exploring Their Mission
AlphaKEK.AI's suite of AI-powered products encompasses conversational and research assistants available on both web and Telegram platforms.
Leveraging real-time data, advanced analytics, and soon, AGI capabilities, these tools provide tailored, actionable insights for individuals and businesses seeking to navigate and capitalize on the dynamic Web3 ecosystem.
Included in AlphaKEK.AI's offerings are multiple AI Apps, such as a crypto news reports analyzer that continuously scans crypto news sources across the internet, generating regular updates and enabling users to create personalized reports.
Additionally, there's an uncensored chatbot and a market sentiment analysis tool.
Moreover, AlphaKEK.AI provides a Telegram bot, enabling users to access the latest crypto reports and engage with the AI chatbot directly through the Telegram platform.
ESelfKey DAO’s Digital Solutions: ESelfKey iD
ESelfKey DAO places a significant emphasis on individuality within its framework. In the ESelfKey Protocol, every member's uniqueness is highly valued as a means of safeguarding their digital identity from theft and forgery.
The goal is to establish a secure environment through AI-Powered Proof of Individuality, enabling valued members to engage in online interactions using trustless and secure methods.
ESelfKey DAO strives to deliver secure digital identity solutions. Leveraging robust credentials in cryptography and blockchain technology, its objectives encompass empowering users with control over their data.
ESelfKey iD: Revolutionizing Digital Identity Management
ESelfKey iD is a cutting-edge technology with a goal to revolutionize online identity verification. By leveraging its innovative on-chain credential system, ESelfKey iD aims to provide a quicker, more secure, and cost-effective alternative to conventional identity verification methods.
This novel approach to online identity verification stems from extensive research, user feedback, and collaborative efforts.
Aligned with the vision of industry experts such as W3C and the authors of the soulbound token paper, ESelfKey DAO aims to establish a modern and potentially more secure identity verification solution.
With ESelfKey iD, users may gain complete autonomy over their digital identities. They may efficiently manage, securely store, and selectively share their credentials with chosen parties.
This may not only foster user confidence but also serve as a deterrent against identity theft and fraudulent activities.
Overall, ESelfKey iD marks a significant advancement in the realm of digital identity verification. It may have the potential to reshape the landscape of online authentication practices.
Partnership Goals
The goal of ESelfKey DAO is to empower individuals to take full control of their private data, enabling them to securely participate in Web3 transactions while preserving their individuality.
Therefore, this collaboration represents a major stride in improving user experience and security within the AlphaKEK ecosystem, as ESelfKey DAO strives to be a pioneer in decentralized identity services.
User Benefits and Perks
This partnership offers several notable benefits, such as:
- Seamless Identity Verification - Users can effortlessly verify their identities using a ESelfKey iD, thanks to the services provided by ESelfKey DAO for AlphaKEK. This is crucial for maintaining compliance and security standards, especially with the introduction of interactive features like airdrops.
- Discounted Services - AlphaKEK users are entitled to a significant 60% discount on ESelfKey's identity verification service by utilizing the code ALPHAKEK. This substantially reduces the entry fee to just $10, making identity verification more accessible.
- Airdrop Incentives - New holders of ESelfKey iD will receive an airdrop of 50 $SELF tokens, the governance token of ESelfKey DAO. This serves as an attractive incentive for users to engage with ESelfKey's ecosystem and participate in its governance processes.
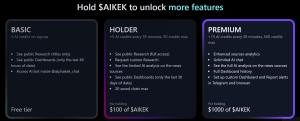
- AlphaKEK Benefits - owning a ESelfKey iD SBT will be equivalent to holding $99 worth of $AIKEK tokens when calculating a user's tier for accessing token-gated AI applications on AlphaKEK.
For instance, if a user already holds $50 worth of $AIKEK tokens, adding a ESelfKey iD SBT to their portfolio will elevate their total value to $149 worth of $AIKEK for the purpose of tier computation.
This would make the user eligible for Tier 2. Higher tiers give access to more powerful tools. Read more here.
Future Potential
The partnership between ESelfKey DAO and AlphaKEK presents mutual advantages, fortifying each entity's position within the digital landscape.
For ESelfKey DAO, the collaboration translates into amplified user adoption. Integration with AlphaKEK widens the scope of potential users, drawing more individuals into ESelfKey DAO's platform and ecosystem.
Furthermore, the partnership enhances the utility of ESelfKey tokens (SELF), incentivizing users to hold and utilize them by offering discounts on particular services and airdrop incentives.
On the other hand, AlphaKEK benefits from strengthened security measures by utilizing ESelfKey DAO's services. This partnership underscores AlphaKEK's commitment to providing a secure and compliant environment for its community, fostering trust among users.
Additionally, AlphaKEK can streamline operations and reduce costs by entrusting identify verification processes to ESelfKey DAO. This may allow ESelfKey DAO to focus on expanding their AI product suite and core competencies
Conclusions
As we transition further into the digital realm and entrust our personal data to online platforms, the demand for advanced digital identity management solutions surges, promising heightened digital security.
The partnership between ESelfKey DAO and AlphaKEK embodies this need for enhanced digital identity management.
Through collaboration, they leverage each other's strengths to drive innovation and instill trust within the community. ESelfKey DAO provides cutting-edge services, reinforcing AlphaKEK's commitment to security and compliance.
In turn, AlphaKEK's focus on expanding AI products allows ESelfKey DAO to concentrate on refining its identity management solutions. This symbiotic relationship not only streamlines operations but also fosters an environment of collaboration and mutual growth.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues.
These tokens should not be purchased for speculative reasons or considered investments. By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>ESelfKey DAO is on a mission to revolutionize the world of digital identity management and it needs your help to spread the word.
As part of its community-driven approach, ESelfKey DAO has introduced the Marketing POD—a dynamic initiative that empowers volunteers to play a vital role in spreading excitement about the project.
In this article, we will delve into the details of the Marketing POD, token generation for social activities, essential guidelines, legal requirements, and the significance of SELF tokens.
Let's embark on this journey to understand how you can contribute to ESelfKey DAO's mission and claim SELF tokens while doing so.
The Marketing POD: An Introduction
The Marketing POD is an exciting new initiative within ESelfKey DAO, designed to harness the power of the community in promoting the project's goals and values.
As a Marketing POD volunteer, you'll have the opportunity to make a significant impact by sharing your enthusiasm for ESelfKey DAO with the world. But how exactly can you get involved? Let's explore the steps to kickstart your journey.
Token Generation for Social Activities
One of the core features of the Marketing POD is the ability for participants to claim SELF tokens for specific social media activities. SELF tokens are an essential component of the ESelfKey DAO ecosystem, and by participating in the Marketing POD, you may claim them while contributing to the project's success. Here's how it works:
Have a ESelfKey.iD
To get started, you must have a SelfKey.iD, which serves as your gateway to participation. If you don't have one yet, you can easily obtain it by following this link.
Spread Excitement
Your primary role as a Marketing POD volunteer is to share your excitement about ESelfKey DAO with the world through social media. You can create posts on platforms such as Twitter, Facebook, or Instagram to promote ESelfKey DAO and its mission.
Eligibility for SELF Tokens
Your efforts won't go unnoticed! Depending on the impact of your social media activities, you may be eligible to claim SELF tokens as a sign of appreciation for your dedication.
Accumulating SELF Tokens
Now let's talk about how you may claim your SELF tokens. By posting about ESelfKey DAO on social media (platforms like Twitter, Facebook, or Instagram), you have the opportunity to accumulate SELF tokens. Here's how it works:
Initial Post
Create an original post about ESelfKey DAO, present it to ESelfKey DAO via a support ticket, and if the post is according to the guidelines, you may claim one SELF token. You can post as many posts as you want, if they are within the guidelines (see below), they might be accepted. Please note that your social media posts must contain the following link "app.selfkey.org".
One-Week Check-In
Return after one week, provide proof that your initial post is still visible, and you may accumulate one more SELF token.
Engagement Bonus
You may claim an additional 0.1 SELF token for every one point of engagement on your post. Engagement includes views, likes, shares, or comments.
Please note that the actual number of SELF tokens you can accumulate is at the sole discretion of ESelfKey DAO. It's essential to understand that the Marketing POD is an experimental initiative. Therefore, the results mentioned here may be subject to change.
Additionally, there are other ways you can participate in initiatives opened by ESelfKey DAO to accumulate SELF tokens. If you’d like to learn more, please follow this link.
Conclusion
The Marketing POD of ESelfKey DAO presents an exciting opportunity for you to actively contribute to the project's success, all while accumulating SELF tokens as a sign of appreciation for your efforts.
By following the guidelines and legal requirements, you can play a crucial role in spreading the word about ESelfKey DAO and its mission.
Remember, participation in the Marketing POD is about creativity, engagement, and adherence to the principles outlined in the ESelfKey DAO Legal Documents and Marketing POD Guidelines. Make sure to stay updated with any changes and always act responsibly and ethically when representing ESelfKey DAO in your social media activities.
Your commitment can make a significant difference in advancing the world of digital identity management.
Join the Marketing POD today and be a part of the ESelfKey DAO community-driven revolution. Together, we can shape the future of digital identity management!
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues.
These tokens should not be purchased for speculative reasons or considered investments. By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>ESelfKey DAO aims to be an active, balanced and positive environment with the goal to facilitate secure interactions between its members.
Because active participation is what makes a DAO thrive, ESelfKey DAO has opened an opportunity for its participants to qualify for SELF tokens. Members may achieve this by helping to identify technical glitches and errors that hinder the optimal use of ESelfKey DAO products.
In this article, we’ll walk through all the steps you need to take in order to take part in this exclusive “bug hunt”. Additionally, we’ll discuss how you may qualify for SELF tokens through your consistent and active participation in the ESelfKey DAO.
Highlights
- The ESelfKey DAO - Benefits and How to Become a Member
- The Bug Bounty
- Other Ways To Qualify For SELF Tokens
- Conclusions
The ESelfKey DAO - Benefits and How to Become a Member
Introduction to the ESelfKey DAO
With a focus on digital identity security and Self-Sovereign Identity (SSID), ESelfKey DAO’s vision is to become a network of individuals with the common goal to contribute to a more secure decentralized future.
As opposed to some centralized systems, which rely on a single authority to control and manage the private data of all individuals which take part of it, ESelfKey DAO strives to have no centralized authority. The aim is to maintain fairness, transparency and equality among its members, by encouraging every individual to participate in the governance process.
Additionally, ESelfKey DAO is focused on minimizing private data exposure during engagement between individuals online. The intent is to enhance digital identity security and mitigate the risks associated with data breaches and identity theft.
For a more in-depth presentation of the ESelfKey DAO, please visit the following link.
How to become a member of the ESelfKey DAO
In order to become a valued member of the ESelfKey DAO you must fulfill certain requirements. For instance, you must be of legal adulthood in your respective country.
Additionally, you must own a ESelfKey iD, which you can obtain simply by visiting this link and connecting your digital wallet.
Please note that in order to obtain a ESelfKey iD, you must provide legal, authentic documents and a selfie as proof of individuality. The purpose of this is to preserve digital security within the DAO.
What is a ESelfKey iD?
A ESelfKey iD is a revolutionary method of digital identity management aimed at enhancing your digital security through the minimization of data sharing, or through the use of zero-knowledge filters.
With a ESelfKey iD, you may participate in the ESelfKey DAO and enjoy the benefits which come with owning and using one, such as the possibility to vote the unlocking of the SELF token.
Additionally, ESelfKey iD owners may qualify for and mint SELF tokens by participating in certain actions aimed at enhancing the security, well-being and overall balance of the DAO.
What makes a DAO thrive is consistent, active participation from its valued members. Therefore, ESelfKey DAO provides this opportunity to its esteemed members to qualify for more SELF by taking part in the Bug Bounty.
The Bug Bounty
What’s the Bug Bounty?
ESelfKey DAO presents the Bug Bounty initiative, inviting members to actively spot and report technical glitches, errors, or bugs within ESelfKey DAO products.
This endeavor seeks to foster community involvement, ensuring ESelfKey DAO’s tools function optimally. It may not only enhance product reliability, but participants also stand a chance to qualify for additional SELF tokens.
In the Bug Bounty, members can submit errors they stumble upon while using ESelfKey DAO products.
Who can submit bugs?
This opportunity is exclusively available only to eligible members of the ESelfKey DAO.
Please note that in order to benefit from this engagement proposal, you must be a ESelfKey iD owner, otherwise you will not qualify for SELF tokens.
How to submit bugs?
At the moment, active members can only submit bugs via the official ESelfKey DAO discord group. If you aren’t part of it, you are welcomed to join by clicking on the following link.
There is a dedicated channel on discord where you can submit errors or bugs and in which you can open a ticket.
Please take note of the following requirements before submitting a bug report:
- Make sure that the bug isn't already listed in the known-bugs channel. Support will not take duplicates into consideration.
- Provide a detailed step-by-step walkthrough and screenshots for bug reproduction. The report needs to be clear and contain precise information on the error.
- Please include essential technical details, such as OS and browser versions, with your report.
- Only bugs found on app.selfkey.org and selfkey.org web apps will be accepted at the moment.
How will support handle the bug reports?
After you’ve made sure you have correctly submitted a bug report, please wait patiently for support to handle the process. If your submission respects the requirements listed above, you will be informed.
Support will check and determine if you qualify for SELF tokens, including the amount of SELF you may be eligible for if your submission is accepted. The severity* of the bug you’ve reported will have a huge influence on determining how much SELF you may qualify for:
- For one minor bug - 1 SELF
- For one medium bug - 3 SELF
- For one critical bug - 10 SELF
*Please note that support will determine the severity of the bug.
Be aware that the quantity of SELF tokens you may be eligible for bug report submissions may vary over time. Stay updated and continue contributing to ensure you benefit from this initiative.
Additionally, if support determines you qualify for SELF, you will see the respective tokens in the DApp.
Other Ways To Qualify For SELF Tokens
Given that decentralization is against having a single authority control and manage the whole system, ESelfKey DAO values participation from all members. The purpose is to include members by inviting them to contribute to the development of the DAO.
Therefore, ESelfKey DAO has opened another opportunity for participants to qualify for SELF tokens.
As stated above, you must be a ESelfKey iD owner in order to participate in the ESelfKey DAO and benefit from the privileges it offers. By introducing an eligible member to the ESelfKey DAO, you may qualify for more SELF.
It is indeed as effortless as that - simply invite another eligible member to become part of the thriving ESelfKey DAO, and you may be eligible for SELF tokens yourself.
Conclusions
DAOs may also provide numerous benefits for its active participants, including the ability to vote for changes in the benefit of the whole community, and have their voice heard.
In turn, active participation and consistent engagement from members are vital for a DAO to function properly and to thrive over time.
If you want to participate in the ESelfKey DAO, get your very own ESelfKey iD and join a community of like-minded individuals!
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues.
These tokens should not be purchased for speculative reasons or considered investments. By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Sybil attacks present a distinct challenge in safeguarding the security and equilibrium of a system, among other types of cybersecurity threats.
The advancement of modern technology has enabled malicious individuals to generate highly convincing fake, digital identities. Therefore, the difficulty in distinguishing between a malevolent bot and a genuine human being becomes especially challenging.
Even when targeting smaller online groups or individuals, counterfeit digital duplicates can inflict significant harm. On a larger scale, within a private system, the infiltration of these malicious replicas can lead to catastrophic consequences. Not only do they endanger individual security, but their calculated intentions have the potential to disrupt the overall security and equilibrium of the entire system.
To combat this issue, ESelfKey is aiming to develop decentralized solutions that may prevent the unauthorized access of these malicious bots to private online accounts and systems. By harnessing the very technology used to create fraudulent identities, ESelfKey's online security methods aim to counterattack Sybil attacks and establish a secure digital ecosystem.
This article provides an in-depth exploration of Sybil attacks and their detrimental impact on the security of digital spaces. Additionally, we’ll elaborate on how ESelfKey strives to reinstate security and balance to private accounts and systems.
Highlights
- Sybil Attacks: The horrifying truth
- The dreadful consequences of Sybil attacks
- Ways in which Sybil attacks may occur
- Sybil attacks on Decentralized Systems
- SelfKey’s Defense against Sybil attacks and Malicious AI
Sybil Attacks: The horrifying truth
In a nutshell
According to literature, Sybil attacks are a method of network-based attacks in which a perpetrator creates multiple fake identities or accounts to gain control or influence over a system.
Interestingly, the term "Sybil" comes from the book "Sybil" by Flora Rheta Schreiber, which portrays a case of multiple personality disorder. In the context of digital security, this refers to a multitude of counterfeit identities which may be controlled by one, single, malicious individual.
What happens in a Sybil attack?
During this kind of cyber attack, bad players create numerous fake identities, also known as Sybil nodes or Sybil identities.
The perpetrators then use them to deceive a network or system into believing that each identity represents a unique and independent user. By controlling multiple identities, the attackers can manipulate the network's behavior, disrupt its operation, or undermine its security.
Who do they target?
Sybil attacks are commonly associated with decentralized systems, such as peer-to-peer networks or blockchain networks. Here, participants rely on the assumption that each identity is unique and represents a distinct user.
By creating a large number of Sybil identities, an attacker can:
- gain disproportionate influence.
- compromise consensus mechanisms.
- launch various malicious activities, such as spreading misinformation, performing Distributed Denial of Service attacks, or controlling a majority of voting power.
Preventing Sybil attacks can be challenging since traditional identification methods may not be effective in decentralized systems that rely on pseudonymous identities. Mitigation strategies often involve:
- implementing reputation systems.
- proof-of-work mechanisms.
- identity verification protocols to establish trust and distinguish between legitimate users and Sybil nodes.
Overall, Sybil attacks pose a significant threat to decentralized systems. Therefore, robust security measures and consensus algorithms are necessary to prevent or minimize their impact.
The dreadful consequences of Sybil Attacks
Sybil attacks can be highly dangerous to digital systems, especially in decentralized networks or systems that rely on trust and consensus. Some reasons why Sybil attacks are considered a significant threat include, but are not limited to the following:
Undermining Consensus
In decentralized networks, like blockchains, where consensus is essential for maintaining integrity and security, a Sybil attack can disrupt the process. By controlling multiple identities, malicious individuals may manipulate voting or decision-making processes. And this may potentially lead to false consensus or control over the network.
Disrupting Network Operations
Sybil attacks can disrupt the normal operation of a network or system. For instance, an attacker may flood the network with fake identities, overwhelming the resources and causing performance degradation or Distributed Denial of Service (DDoS) attacks.
Spreading Misinformation
Bad players can leverage Sybil identities to spread false information or manipulate the perception of consensus. By taking control of a significant number of identities, they can amplify their influence and create the illusion of broad support for malicious content.
Exploiting Trust and Reputation Systems
Many digital systems rely on trust and reputation systems to establish credibility and make informed decisions. During a Sybil attack, a perpetrator can create a large number of fake identities with positive reputations. This way, they may mislead others into trusting them and granting them privileges they shouldn't have.
Security Risks
Lastly, Sybil attacks can compromise user security. For instance, if a Sybil attacker gains control over multiple identities, they may have access to sensitive user information, financial data, or private communications. Horrifyingly, this may lead to identity theft, fraud, or unauthorized access to personal accounts.
Because the consequences of Sybil attacks can be devastating to a decentralized system, it’s crucial for certain security measures to be implemented, such as:
- Identity verification protocols.
- Reputation Systems.
- Proof-of-Work mechanisms.
- Consensus algorithms that incentivize honest behavior.
By doing so, individuals may help minimize the risks and consequences of Sybil attacks, before they corrupt whole systems.
In spite of all these security methods, though, developing strong defenses against Sybil attacks remains a continuous challenge. Therefore, constant vigilance and research are necessary to ensure the security and integrity of digital systems.
Ways in which Sybil attacks may occur
Unlike other methods of cyberattacks, which target one type of individual in particular or have a single scope, Sybil attacks can occur in many ways, with many specific purposes. Let us examine a few of them.
Distributed Denial of Service (DDoS) Attacks
In this type of attack, malicious individuals can create multiple Sybil nodes and use them to flood a target system or network with requests. This process can overwhelm the system’s resources and cause it to become unresponsive. And, by controlling a large number of identities, the attackers can amplify the impact of the attack.
Influence Manipulation in Social Networks
In social networks, attackers can create multiple fake profiles and use them to manipulate discussions, spread propaganda, or artificially inflate the popularity of certain content. Because they can appear as different individuals, the attackers can exert undue influence and manipulate the perception of consensus.
Blockchain Network Attacks
In blockchain networks, malicious individuals may create numerous Sybil identities to gain control over the consensus process. By controlling a majority of identities or computing power (known as a Sybil attack on proof-of-work), the attackers may:
- manipulate transaction verification.
- double-spend coins.
- launch other malicious activities that undermine the security and integrity of the blockchain.
Spamming and Reputation Manipulation
In online platforms that rely on reputation systems, such as e-commerce or review websites, an attacker can create multiple Sybil accounts to spam or manipulate ratings and reviews.
With the aid of numerous, fake identities, the attacker can artificially inflate or deflate the reputation of products, services, or individuals. And, this way, they can mislead other users and affect their decision-making.
Influence in Online Voting Systems
In online voting systems or opinion polls, attackers may create multiple Sybil identities to sway the results by casting multiple votes or skewing the perception of public opinion. In doing so, the perpetrators can distort the outcome and compromise the integrity of the voting process.
These examples shed a light on how Sybil attacks can be used to manipulate, disrupt, or deceive various digital systems. Preventing and minimizing these attacks often requires implementing strong security measures, such as:
- identity verification protocols.
- reputation systems.
- consensus mechanisms that can differentiate between genuine users and Sybil nodes.
Sybil Attacks against Decentralized Systems
A brief introduction to Decentralized Systems
Decentralized systems are computing or network architectures in which authority, control, and decision-making are distributed among multiple nodes or participants. This comes in stark contrast to centralized systems, in which a single entity or central server has authority.
In decentralized systems, no single entity has complete control or ownership over the entire system, and participants collaborate to achieve shared goals.
Why do Sybil attacks target decentralized systems?
Sybil attacks specifically target decentralized systems because these systems rely on the assumption that each node or participant represents a unique and independent entity.
By creating multiple fake identities, or Sybil nodes, malicious players can exploit the inherent trust and consensus mechanisms of decentralized systems. And this, in turn, could lead to various malicious activities.
Let us discuss a few reasons why Sybil attacks are particularly effective against decentralized systems.
1. Exploiting Consensus Mechanisms
Decentralized systems often employ consensus mechanisms to achieve agreement among participants. Sybil attacks can undermine these mechanisms by creating a large number of fake identities that skew the consensus process. This way, attackers can manipulate voting, decision-making, or transaction verification, compromising the integrity and security of the system.
2. Gaining Disproportionate Influence
What’s commonly known about decentralized systems is that they strive to give equal power and influence to each participant. However, in a Sybil attack, a perpetrator can create numerous Sybil nodes, effectively giving them disproportionate influence over the system. This can enable the attacker to exert control, manipulate perceptions, or disrupt the normal operation of the network.
3. Exploiting Trust and Pseudonymity
Many decentralized systems rely on pseudonymous identities to protect user privacy. Unfortunately, this anonymity also creates opportunities for Sybil attacks.
Malicious individuals can create multiple fake identities that are almost indistinguishable from legitimate ones. And using these, they can deceive others into trusting them and granting them privileges or access they shouldn't have.
4. Undermining Network Resilience
Decentralized systems often emphasize resilience and fault tolerance. But, a Sybil attack can compromise these attributes by flooding the network with fake identities.
An attacker can overwhelm resources, disrupt communication, or launch Distributed Denial of Service (DDoS) attacks, undermining the stability and availability of the system.
Due to these factors, Sybil attacks pose a significant threat to decentralized systems. In turn, this highlights the importance of implementing strong security measures, to prevent and reduce the risks associated with Sybil attacks.
SelfKey’s Defense against Sybil Attacks and Malicious AI
The significance of digital security is amplified in decentralized systems, given the distinct challenges and vulnerabilities they entail. Some crucial aspects that require strong security measures in decentralized environments include, but are not limited to:
- preserving data integrity.
- upholding consensus integrity.
- mitigating network threats.
- safeguarding digital assets.
- fostering trust among participants.
Preventing Sybil attacks in decentralized systems can be challenging, but there are several measures that can help mitigate the risk. Let us discuss some strategies which may prevent Sybil attacks.
Identity Verification
The first step is implementing strong identity verification mechanisms to ensure that participants in the decentralized system are unique and authentic individuals. This can include verification through trusted third parties, KYC (Know Your Customer) procedures, or reputation systems that assess the trustworthiness of participants based on their past behavior.
Given this, ESelfKey proposes ESelfKey iD as a possible solution to combat identity theft and digital duplicates. ESelfKey iD uses the power of Artificial Intelligence (AI) to detect fake, AI-generated digital identities and identity thieves, which could considerably lower the risks associated with Sybil attacks.
Sybil Resistance Mechanisms
Another important step is to design the decentralized system with built-in Sybil resistance mechanisms. These mechanisms aim to make it difficult or costly for attackers to create and control a large number of fake identities.
Examples of Sybil resistance mechanisms include proof-of-work or proof-of-stake protocols, where participants must provide computational resources or stake tokens to participate in the system.
In the ESelfKey DAO, members may mint SELF tokens as a part of the proof-of-individuality locking protocol. Again, this is developed utilizing the power of AI to gain more accurate and quick results, as AI can read and analyze patterns which may be impossible for the naked human eye to detect.
Through this process, ESelfKey aims to prevent duplicate accounts, malicious bots, or identity thieves from accessing private accounts or systems. Locking, in this context, is done solely with the purpose of increasing digital security.
Reputation Systems
Implementing reputation systems that track and evaluate the behavior of participants in the decentralized system is another crucial step. Reputation systems can help identify suspicious or malicious activities, making it harder for attackers to blend in and gain influence.
Participants with positive reputations may be given more privileges, while those with negative reputations may be subject to additional scrutiny.
For this purpose, ESelfKey has developed an engagement system which offers active members the opportunity to mint SELF tokens for their contribution to the DAO.
Consensus Algorithms
Consensus mechanisms like Proof of Stake (PoS) or Practical Byzantine Fault Tolerance (PBFT) can require participants to prove ownership of a significant stake. Additionally, they may require them to demonstrate a high level of computational resources. This may make it more challenging for attackers to create a large number of identities and control the network.
Randomized Node Selection
Another method which may be efficient in preventing Sybil attacks is to incorporate randomized node selection in the network's protocols and algorithms. By randomly selecting nodes for tasks, such as voting or validation, the likelihood of multiple fake identities controlled by the same attacker being chosen is reduced, making Sybil attacks less effective.
Network Monitoring and Analysis
Analyzing network traffic, node behavior, and communication patterns can help identify patterns that are indicative of Sybil attacks. Therefore, employing network monitoring tools and techniques to detect unusual or suspicious activities is crucial.
Community Engagement and Auditing
Lastly, encouraging active participation from the community in detecting and reporting potential Sybil attacks is vital. It’s also important to conduct regular audits and security assessments to identify vulnerabilities and address them promptly.
Engaging the community can create a collaborative effort to identify and mitigate the risk of Sybil attacks.
Conclusions
It's important to note that preventing Sybil attacks entirely is challenging, and a combination of preventive measures is often necessary. The specific prevention techniques employed will depend on the nature of the decentralized system, its objectives, and the potential threat landscape.
What’s vital is for the community to work together and for members of a DAO to be consistently active. Not only to keep the DAO alive, but also to protect their common goals and the security and balance of the system they are a part of.
ESelfKey DAO aims to become a digital environment which may offer both security and convenience. By utilizing the amazing potential of AI, and with the contribution of its participants, ESelfKey strives to prevent cyber attacks that threaten the security and balance of our digital future.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details. The term "staking" is used solely as it is described here and does not mean any investment or similar activities.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>With the rapid integration of modern technology into our daily lives, it has become increasingly important to grasp the concepts that will shape our digital future. One such concept that holds immense significance is tokenization.
This transformative technology has the potential to revolutionize various industries, including finance, real estate, supply chain management, and intellectual property rights. However, while enjoying its benefits, it is vital to consider that tokenization also poses certain challenges.
Understanding and addressing these challenges will be crucial to fully harness the benefits of tokenization. It is also essential to ensure the protection of individuals' rights and maintain the integrity of the digital ecosystem.
However, the introduction of innovative technology has historically encountered resistance within society. And, the human inclination to resist change stems from a lack of understanding about new concepts and their functionalities.
To address this challenge, ESelfKey aims to offer a comprehensive guide on tokenization. The goal is to enlighten individuals about the intricacies of tokenization, including its benefits and the challenges it may present as we embark on a new digital era.
With knowledge and awareness, we can collectively embrace this cutting-edge technology and pave the way for a more inclusive and efficient digital society.
Highlights
- What is Tokenization?
- The Benefits of Tokenization
- Tokenization: Challenges and Risks
- A Glimpse into ESelfKey’s Protocol
- Conclusions
What is Tokenization?
A brief definition
Tokenization, in the context of data security, involves the substitution of sensitive data with a non-sensitive equivalent, known as a token. The purpose of tokenization is to render the original data meaningless and devoid of exploitable value. Instead, a token is generated, which serves as a reference point linking back to the sensitive data through a tokenization system.
The tokenization process is designed with the aim to enhance data protection by reducing the risk associated with storing or transmitting sensitive information. By replacing sensitive data, such as credit card numbers or personal identification details, with tokens, the likelihood of unauthorized access or misuse of the original data may be significantly minimized.
The tokenization system manages the mapping between the tokens and their corresponding sensitive data, ensuring that the original information can be retrieved when needed by authorized entities. This system may provide a secure and efficient way to handle sensitive data, reducing the exposure to potential breaches or theft.
Overall, tokenization plays a vital role in safeguarding sensitive information, preserving data privacy, and maintaining the integrity of systems that handle sensitive data elements.
Tokens Explained
Tokens may function as digital assets or representations of value that are built on top of existing blockchain networks. They can serve various purposes and operate within specific ecosystems.
Technically, tokens are programmable digital objects that are created and managed through smart contracts. These contracts dictate the rules and behaviors of the tokens, such as their supply, transferability, and functionality.
Individuals can create tokens on different blockchain platforms, such as Ethereum, Binance Smart Chain, or Solana, using their respective token standards like ERC-20, BEP-20, or SPL. And, depending on their design, they can have different functionalities.
For instance, tokens can:
- Be used as a medium of exchange and stores of value.
- Represent ownership rights in a particular asset or project.
- Have utility functions within decentralized applications (DApps), enabling access to specific features or services.
Overall, tokens operate within the framework of blockchain technology. They offer a flexible and programmable way to represent and exchange data or value within digital ecosystems.
Types of Tokens
In addition to the general definitions mentioned earlier, there are specific categories of cryptoassets that include the word "token" in their name. Here are a few examples:
- DeFi tokens refer to crypto tokens issued by decentralized finance protocols, which aim to replicate traditional financial functions. These tokens serve multiple purposes within their respective protocols and can be traded or held like any other cryptocurrency. For instance, individuals may use them for lending, saving, insurance, and trading.
- Governance tokens are specialized tokens which grant holders the ability to participate in decision-making processes for a protocol or application. As decentralized platforms lack central authorities or boards of directors, governance tokens provide voting rights.
- Non-Fungible Tokens (NFTs) represent ownership rights to unique digital or real-world assets. They have been utilized to combat unauthorized copying and sharing of digital creations. Additionally, NFTs have gained popularity in the art world for issuing limited editions of digital artwork or selling exclusive virtual assets like rare items in video games.
- Finally, security tokens are cryptoassets which are designed to function as the cryptocurrency equivalent of traditional securities, such as stocks and bonds. Security tokens enable the sale of shares in companies or other ventures, including real estate, without the involvement of brokers. Major companies and startups are exploring security tokens as an alternative fundraising method.
By familiarizing oneself with these different categories of tokens, one can gain a better understanding of the diverse applications and functionalities within the crypto space.
The difference between Crypto and Tokenization
The difference between cryptocurrency and tokenization lies in their underlying concepts and functionalities.
Cryptocurrency refers to digital currencies that utilize cryptographic techniques to secure transactions and control the creation of new units. Examples of cryptocurrencies include Bitcoin (BTC) and Ethereum (ETH).
Cryptocurrencies typically operate as independent entities with their own blockchain networks. They can function as a medium of exchange, a store of value, or a unit of account.
On the other hand, tokenization is the process of converting data, real-world assets, rights, or functionalities into digital tokens that exist and operate on a blockchain. Tokens can represent various forms of value, such as ownership rights, access to services, or participation in a project.
In summary, cryptocurrency refers to digital currencies that operate independently on their respective blockchain networks, while tokenization involves the creation and representation of data, assets or functionalities as digital tokens within a specific platform or ecosystem.
The Benefits of Tokenization
Tokenization offers several benefits for data security and efficiency. Here are a few key advantages of tokenization, which we will discuss more thoroughly below:
- Enhanced Data Security
- Improved Data Processing Efficiency
- Simplified Data Management and Migration
Enhanced Data Security
Tokenization helps protect sensitive information by replacing it with randomly generated tokens that have no intrinsic value or meaning. Unlike encryption, tokenization removes the need to store sensitive data, significantly reducing the risk of data breaches. Even if a hacker gains access to the tokenized data, it is almost impossible to reverse-engineer the original information.
Improved Data Processing Efficiency
Tokenization accelerates data processing and retrieval by replacing long and complex data strings with shorter tokens. These tokens are easier and faster to search, index, and analyze. And this leads to improved performance and efficiency in data-intensive applications such as databases, data warehousing, and big data analytics.
Simplified Data Management and Migration
Lastly, tokenization facilitates data management and migration processes, particularly when transitioning between different systems or databases. When migrating data, tokens can be used to maintain data integrity and relationships while ensuring sensitive information remains secure.
Additionally, tokenization simplifies data integration, as systems can exchange tokens instead of transferring actual data. This may reduce the complexity and overhead of data sharing.
All in all, tokenization may offer notable security advantages. However, it is crucial to prioritize the management and protection of the tokenization system itself. This will ensure comprehensive security throughout the process.
Tokenization: Challenges and Risks
While tokenization offers numerous benefits, there are also potential risks associated with its implementation, for instance:
- Dependency on Tokenization System
- Token Reversal Attacks
- Token Mapping Vulnerabilities
- Single Point of Failure
Dependency on Tokenization System
Organizations adopting tokenization may become reliant on the tokenization system and infrastructure. If the system experiences a breach, suffers from downtime, or becomes unavailable, it can disrupt operations and impact business continuity.
It is therefore crucial to implement robust security measures and backup systems to mitigate such risks.
Token Reversal Attacks
Although tokenized data is not directly reversible, attackers may attempt token reversal attacks by exploiting vulnerabilities in the tokenization system or its implementation. If successful, these attacks could potentially derive sensitive information from the tokens. And, in turn, it may undermine the security benefits of tokenization.
Vigilance in system design and implementation, as well as regular security audits, can help mitigate this risk.
Token Mapping Vulnerabilities
Tokenization relies on a mapping or lookup table that connects tokens to their original data. If malicious individuals compromise this mapping table, they may gain access to the original sensitive information.
Robust security measures are therefore essential to protect against this risk, such as:
- strong access controls.
- encryption of the mapping table
- secure key management.
Single Point of Failure
Centralizing tokenization processes introduces a single point of failure. If the tokenization system or central repository is compromised, it can have widespread implications across the organization, potentially exposing sensitive data or disrupting operations.
Implementing redundancy, disaster recovery mechanisms, and distributed tokenization systems can help mitigate this risk.
All in all, it's important to note that while these risks exist, there are methods which may mitigate them and maximize the benefits of tokenization. These methods include, but are not limited to:
- implementing proper security measures.
- conducting regular assessments.
- adhering to best practices.
A Glimpse into ESelfKey’s Protocol
When developing decentralized solutions, ESelfKey places great emphasis on digital identity privacy and security. The vision is to create a more secure decentralized network, in which members may be able to exercise their Self Sovereign Identity rights.
ESelfKey DAO may be such a platform by treating its members with transparency, equality, and fairness. Within the ESelfKey Protocol, there are currently two tokens which serve as pivotal elements: KEY and SELF.
KEY: A Brief Introduction
Utility tokens derive their value from their utility or functionality within the ecosystem they are associated with. One may use them within the platform to exchange for goods or services, participate in voting or governance processes, access premium features, or facilitate interactions.
The KEY token may find utility in various ways, including:
- Serving as a method of exchange for services within the ESelfKey Protocol.
- Enabling users to lock their credentials more securely.
- Empowering members to govern the ESelfKey DAO.
- Equipping users with essential tools which may allow them to take charge of their digital identity and increase privacy protection.
The Purpose of SELF
While KEY remains the vital utility token to lock credentials, ESelfKey introduces the SELF tokens to facilitate tracking of an individual's locked credentials and their duration.
Having access to the ESelfKey DAO may enable users to mint their own SELF tokens. Individuals may use these tokens for various purposes and services on the ESelfKey platform.
Here are some notable attributes of SELF tokens:
- Individuals who successfully lock a real identity may mint SELF tokens.
- SELF tokens may serve as a metric for reputation measurement.
- As a reputation signal, they may strengthen legitimate credentials and help identify illegitimate ones.
- Users themselves may mint SELF tokens, and they hold no inherent value.
- SELF tokens may also serve as a governance mechanism, granting influence to those who use the platform, accumulate reputation, or engage in "identity mining" to enhance platform security.
- As users lock valid credentials, they accumulate reputation in the form of SELF tokens.
By introducing SELF tokens, ESelfKey may enhance the ecosystem by providing individuals with a way to monitor their locked credentials and reputation. At the same time, it may promote the integrity and security of the platform.
Locking for Digital Safety
By locking KEY tokens on their credentials, users may mint SELF tokens. Locking credentials may be a way for individuals to demonstrate confidence in the accuracy of their data. This, in turn, may increase the validity of their credentials.
The purpose of locking, therefore, is to enhance digital security. This may prevent data breaches, identity theft, and unlawful attempts by malicious bots to infiltrate your private online accounts and systems.
Conclusions
The rapid progress of modern technology constantly astonishes us, bringing forth opportunities for knowledge, efficiency, communication, and speed.
Tokenization, a relatively new concept, has the potential to simplify private data management and enhance online security through encryption methods, offering benefits in terms of privacy, security, speed, and efficiency.
Understanding this evolving concept becomes crucial in order to stay informed about its advancements and leverage its advantages without compromising our digital identities and online security.
For these purposes, ESelfKey aims to educate people about digital safety and introduce them to innovative concepts and technologies that can enhance online privacy and security. Knowledge is vital in order to prevent online attacks aimed at our digital identities, therefore staying up to date with relevant news on this topic and spreading awareness is important.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
SelfKey's staking feature is different from traditional staking you might find in other crypto projects. It does not mean any investment or similar activities. Instead, it's a mechanism designed to strengthen the ESelfKey ecosystem and support users' digital identities.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Throughout the past several decades, modern technology has evolved at amazing speeds, with the latest innovation being introduced as ‘Web3’.
The purpose of these changes is to enhance the benefits that cutting-edge technology already brings us. However, as we enjoy the new technological trends, it’s important to understand the concept of Web3 at its core, with the good and the bad.
Perhaps most individuals are accustomed to the internet in its Web2 form, because it has been the most common platform for years now. But despite its convenience and familiarity, the centralized nature of Web2 limits its capabilities. Because of this, Web3 was designed with a focus on decentralization, individuality, and security.
These concepts align with ESelfKey’s visions of a decentralized future, in which individuals may be able to exercise their SSID rights, as well as engage in a more secure, privacy-oriented environment. Web3 could be a network that may allow individuals the freedom to truly own their domains, ideas, and digital identities.
While all of this may be true, it’s important to recognize the risks which may come with the adoption of Web3 in our daily lives. It’s no longer a secret that cybercriminals lurk at every corner of these digital spaces, with victims ranging from common folk to large, seemingly powerful systems.
Given this, it’s important for individuals to stay informed with technology’s fast-paced evolution, the advantages and especially the challenges which come with it.
This article aims to provide a comprehensive guide on what Web3 is, how it works, the benefits it brings compared to Web2, as well as the risks. Additionally, we will discuss ESelfKey’s proposed decentralized solutions which may enhance digital security as we step into Web3.
Highlights
- An Introduction to Web3
- Web3 Benefits and Opportunities
- The Dark Side of Web3
- Web3 and ESelfKey
- Conclusions
An Introduction to Web3
Evolution is natural in many aspects of life. With modern technology, however, it’s especially beneficial when networking and artificial intelligence can considerably enhance the way society functions. Let us discover the concept of Web3, what it is, and how it can affect our daily lives.
What is Web3?
Web3, or Web 3.0, represents a new vision for the next phase of the World Wide Web. It aims to integrate principles like decentralization, blockchain advancements, and token-driven economies.
The range of emerging technologies and projects it encompasses include, but are not limited to:
- decentralized finance (DeFi)
- non-fungible tokens (NFTs)
- decentralized applications (dApps)
At its core, Web3 envisions a future where individuals have greater sovereignty over their digital lives. Where trust and transparency are built into the very fabric of the internet.
Web2 to Web3: How different are they?
Web2 is the current version of the internet, encompassing all the technologies and projects people are accustomed to nowadays. While Web2 has proven to be an inclusive and dynamic form of the web, it has its limitations due to its centralized nature. In this context, Web3 aims to enhance user freedom, privacy, and security.
There are many differences between Web2 and Web3. For now, let us explore two of the most prominent aspects which set them apart:
- Centralization vs. Decentralization
- Data Ownership and Privacy
Centralization vs. Decentralization
Web2 platforms and services are predominantly centralized, meaning they rely on centralized servers and intermediaries to operate. Companies like Google, Facebook, and Amazon control and manage user data and have the authority to set rules and policies. Because of this, users have limited control over their data and are dependent on these centralized entities.
Web3, on the other hand, emphasizes decentralization. It operates on peer-to-peer networks and blockchain technology, where data is distributed across multiple nodes. Users have greater control over their data and can interact directly with decentralized applications (dApps) without the need for intermediaries. Smart contracts and consensus mechanisms enable decentralized governance models where the community collectively makes decisions, instead of relying on a single authority.
Data Ownership and Privacy
In Web2, user data is often collected, stored, and controlled by centralized platforms. Users typically agree to terms and conditions that grant these platforms the right to use and monetize their data. Privacy concerns arise due to the potential for data breaches, surveillance, and unauthorized access to personal information.
Web3, on the other hand, prioritizes user ownership and control over data. With decentralized storage systems and encryption mechanisms, users may securely store and manage their own data.
Blockchain technology provides transparency and auditability, which may reduce the risk of unauthorized manipulation or access. Users have the ability to grant and revoke access to their data on a case-by-case basis, enhancing privacy and data sovereignty.
All in all, these differences highlight the shift from a centralized and controlled web to a more decentralized, user-centric, and economically empowering Web3 ecosystem.
Web3 Benefits and Opportunities
Due to its decentralized nature, and not only, Web3 can offer a multitude of benefits and opportunities. Let’s examine a few:
- Decentralization and Trust
- Data Ownership and Privacy
- Economic Empowerment
- Interoperability and Seamless Experiences
- Community Governance and Collaboration
Decentralization and Trust
Web3 aims to decentralize power and eliminate the need for intermediaries by leveraging blockchain technology. This can result in a more trustless and transparent online environment. Users may interact directly with each other and verify transactions without relying on centralized authorities.
For instance, ESelfKey DAO aims to be a decentralized and trustless digital environment, due to its emphasis on limited data sharing.
Data Ownership and Privacy
One thing that Web3 prioritizes is user ownership and control over personal data. This is also known as Self Sovereignty, and it aims to reduce the risk of data breaches by enabling individuals to be the sole owners of their data.
Through decentralized storage systems and encryption mechanisms, users may securely store and manage their own data. They can selectively grant access to their data and have more control over how it is used and shared.
This shift towards user-centric data ownership may enhance privacy and empower individuals to protect their personal information.
Economic Empowerment
Another advantage of Web3 is that it introduces new economic models enabled by cryptocurrencies and tokens. This may allow individuals to participate in decentralized finance (DeFi) systems, where they can lend, borrow, and invest without relying on traditional financial intermediaries.
Tokenization and the concept of ownership over digital assets may open new opportunities for creators, artists, and content providers to monetize their work directly. By eliminating the need for intermediaries, Web3 could potentially create more equitable economic systems.
Interoperability and Seamless Experiences
Web3 aims to promote interoperability between different blockchain networks and protocols. This means that users may seamlessly interact with various decentralized applications (dApps) and move assets across different platforms without facing barriers or restrictions. It allows for a more connected and cohesive ecosystem where users may access a wide range of services and functionalities.
To aid this, ESelfKey proposes ESelfKey iD as a decentralized solution which may enhance digital security as individuals operate in these platforms.
Community Governance and Collaboration
Finally, Web3 enables decentralized governance models through mechanisms like smart contracts and decentralized autonomous organizations (DAOs). This allows users to have a say in the decision-making processes of the platforms they engage with.
Users can participate in voting, propose changes, and contribute to the development and evolution of the platforms they use. And this fosters a sense of community ownership and collaboration, empowering users to shape the direction of the platforms and protocols they rely on.
All in all, these benefits highlight Web3’s potential to transform the internet into a more user-centric, transparent, and inclusive ecosystem.
However, it's important to note that Web3 is still an emerging concept. Therefore, its actual realization and impact will depend on the development and adoption of relevant technologies and applications.
The Dark Side of Web3
While Web3 brings potential benefits, it also presents certain risks and challenges that need to be considered. It’s important to be aware of these challenges in order to take preventive measures and remain vigilant.
Here are five potential risks that may occur with Web3:
- Security and Privacy Concerns
- Bots and Maliciously-used AI
- User Responsibility and Risks
Security and Privacy Concerns
As Web3 relies heavily on blockchain technology and decentralized systems, it introduces unique security and privacy considerations. Although blockchain is renowned for its robust security, vulnerabilities and exploits can still occur.
Additionally, decentralized storage and peer-to-peer networks may face privacy challenges. Therefore, they require careful attention to encryption, data protection, and identity management to ensure user privacy.
Bots and Maliciously-used AI
In Web3, identity and reputation systems can be compromised by bots through sybil attacks. Bots can create multiple fake identities to gain influence, voting power, or access to certain resources within decentralized networks. This can undermine the trust and fairness of the system.
Bad players can also program AI to distribute spam messages or engage in phishing attacks within decentralized communication platforms. These attacks aim to deceive users into sharing sensitive information or clicking on malicious links, compromising their security and privacy.
User Responsibility and Risks
Web3 shifts more responsibility onto users, as they have greater control over their digital assets and interactions. With increased control comes increased risk, as users are solely responsible for managing their private keys. This includes securing their wallets, and avoiding scams or fraudulent activities.
User error or negligence can result in irreversible loss of funds or unauthorized access to personal data, necessitating heightened user awareness and education.
It is important to recognize these risks and address them proactively. One can do this through responsible development, regulatory frameworks, user education, and sustainable practices. The purpose is to maximize the promising benefits of Web3 while mitigating potential downsides.
Web3 and ESelfKey
Web3 could considerably enhance the internet as we know it. Through decentralization and user-centricity, it could become a digital space in which users may engage with one another without limitations to their privacy and individuality.
This aligns with ESelfKey's focus on individuality, as well as its aim to develop decentralized solutions that may increase digital security. The goal is for individuals to enjoy the benefits Web3 may offer, without having to constantly worry about the safety of their private data.
Let’s look at a few of ESelfKey’s proposed decentralized solutions which may enable individuals to operate in Web3 more securely.
Self Sovereign Identity (SSID)
SSID is an innovative method of managing online identities, which aims to put the user in control of their digital identity.
ESelfKey aims to incorporate SSID into its decentralized solutions, which may ensure that users have complete autonomy over their personal data at all times. Enabling individuals to fully own and manage their private information may significantly diminish the risks associated with data breaches and identity theft.
The absence of third-party involvement allows users to have complete visibility and control over the storage and accessibility of their data. And this may enable them to make informed decisions regarding its usage and sharing.
ESelfKey DAO
ESelfKey DAO aims to be a trustless and decentralized digital environment, which may enable individuals to exercise their SSID rights. By limiting the private data which they share, individuals may reduce the risk of data breaches and identity theft, and this may enable them to operate in the DAO more confidently.
Another of ESelfKey DAO’s main purposes is to treat individuals with fairness, equality, and transparency. It aims to take every member’s propositions, thoughts, and opinions into consideration, to facilitate a decision-making process which is responsive to users’ needs.
ESelfKey ID
ESelfKey iD was designed with SSID in mind, with a strong emphasis on digital privacy and security. Not only that, but individuals may use it for accessing both Web2 and Web3 projects and applications.
ESelfKey provides a guide on how ESelfKey iD may be used for online identity verification, as well as the benefits it may bring.
Along with increased privacy and security, ESelfKey iD also aims to enable individuals to truly express themselves in current and future online spaces. By attaching a Normie to ESelfKey iD as a profile picture, users may showcase their personality, hobbies, and uniqueness.
This is to promote individuality, so that users may be able to confidently show their originality in cyberspace, without divulging sensitive or personal information.
Conclusions
Whether we’re talking about Web2, Web3, or any other future version of the internet, it’s important to always keep privacy and security in mind. These innovative online spaces can be quite disarming due to their immersive nature and the illusion of choice when it comes to the safety of our personal data.
For this reason, ESelfKey aims to develop decentralized solutions which may offer the convenience of centralized systems, with the benefits of decentralized systems. In the meantime, it’s vital to remain informed about the potential risks, and take preventive measures to avoid putting our digital identities in danger.
By prioritizing digital security, ESelfKey strives to empower individuals to embrace technology without sacrificing the safety of their digital identity.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>In the present, the vast majority of individuals are familiar with modern technology, the internet, and the notion of online identity.
Even though digitization may have not reached every corner of the world yet, most people are no strangers to these concepts. Especially among the younger generation, many have already established a digital presence and have been active online for years.
The integration of the digital realm into people's lives has unlocked immense opportunities for education, communication, and work. Technological advancements continue to push boundaries each year, with innovations like the metaverse and its captivating shared virtual spaces.
However, it’s important for individuals to grasp the concept of online identity, recognizing both its advantages and the potential risks it entails. Among these risks, identity theft stands out as one of the most impactful.
Considering the long-lasting and potentially devastating consequences of identity theft, it’s very important for people to educate themselves on the matter. Additionally, it’s crucial to raise awareness about this issue. Doing so can greatly empower individuals and help them protect their online identities from cyberattacks.
In this article, we will thoroughly discuss the concept of online identity and how it works, with the good and the bad. Additionally, we will discuss how ESelfKey may enhance security and privacy for individuals operating in the digital realm.
Highlights
- What is Online Identity?
- How Online Identity Works
- The Benefits of Having an Online Identity
- Online Identity Risks and Challenges
- How ESelfKey May Improve your Online Identity Management
- Conclusions
What is Online Identity?
A brief definition
The concept of online identity refers to a persona which people establish for themselves on the internet. Also called internet identity, online personality, or internet persona, it may be used in online communities and websites. It can also be a way of intentionally showing and representing oneself.
Although some people choose to use their real names online, some internet users prefer to be anonymous. They identify themselves by means of pseudonyms, which reveal varying amounts of personally identifiable information.
Additionally, an online identity may even be determined by a user's relationship to a certain social group they are a part of online.
Online Identity vs Digital Identity
Even though online identity and digital identity are often found in the same context, there is a notable distinction between them. The difference between online identity and digital identity lies in their scope and focus.
Online identity specifically pertains to the persona and representation of a person in the online realm. It encompasses the social identity an individual establishes in online communities, websites, and social media platforms.
It includes elements such as:
- Usernames and profiles.
- Personal information.
- Digital footprints.
All in all, it is the perception others have of the individual based on their online presence.
Digital identity, on the other hand, is a broader concept that encompasses the information and attributes associated with any entity, not limited to individuals. It extends beyond just personal online presence and encompasses a wider range of entities and their attributes.
This includes organizational identities, system identities, device identities, and more. It focuses on how entities are identified, authenticated, and represented in the digital domain.
In simple terms, online identity refers to how a person appears and acts online, while digital identity is a broader concept that includes representing any entity in the digital world, such as people, organizations, apps, and devices.
Digital Footprints
While navigating the internet, it's important to remember that our online actions can have lasting effects on specific websites. These effects are referred to as digital footprints.
Digital footprints are the marks or records of our online activities and interactions that remain after using digital devices and platforms. They can include different types of data, like personal information, online behaviors, communications, and contributions.
Some examples include, but are not limited to:
- Social Media Posts
- Web Browsing History
- Online Purchases
- Email Communication
- Online Profiles and Accounts
Social Media Posts
Any content shared on social media platforms, including photos, videos, comments, and likes, contributes to a person's digital footprint. These posts can provide insights into their interests, opinions, and activities.
Web Browsing History
Every website visited and the search queries made leave a digital trace in the form of browsing history. It can include information about the types of websites visited, articles read, products searched for, and online services used.
Online Purchases
When making online purchases, individuals leave a digital footprint through transaction records. This can include payment information, shipping addresses, and product preferences. This data can be collected and analyzed to understand consumer behavior and tailor personalized advertisements.
Email Communication
Emails sent and received, including attachments, provide a digital trail of personal and professional conversations. The content of these emails can reveal information about relationships, affiliations, and communication patterns.
Online Profiles and Accounts
The creation and maintenance of online profiles on platforms such as LinkedIn, dating websites, or gaming communities contribute to a person's digital footprint. These profiles often contain personal information, employment history, educational background, and connections. And they form a digital representation of an individual's identity.
It's important to note that digital footprints can have implications for privacy, security, and reputation management. The data accumulated over time can be used for various purposes, including targeted advertising, data analysis, and even potential misuse.
Because of this, it’s vital that individuals take extra caution when browsing the internet, especially when sharing private information. Even websites that appear trustworthy may be at risk of data breaches.
How Online Identity Works
On a daily basis, individuals rely on their online identities to access various applications. Certain websites play a pivotal role in everyday work, communication, and education. However, there are also online domains that serve as sources of entertainment or offer delightful distractions.
Here are a few examples in which people make use of their online identities:
- Social Media
- Online Gaming
- Professional Networks
- Online Communities and Forums
- E-commerce and Online Shopping
Now, let's take a moment to briefly discuss them.
Social Media
On platforms like Facebook, Twitter, or Instagram, online identity is built through the creation of profiles. This may also include sharing personal information, posting content, and engaging with others. For example, a person's online identity on Instagram might include their username, profile picture, bio, and the photos or videos they share.
Online Gaming
In the realm of online gaming, players often create unique usernames, avatars, and profiles that represent their gaming persona. Their online identity in this context is influenced by their gaming achievements, playstyle, interactions with other players, and reputation within the gaming community.
Professional Networks
Platforms like LinkedIn focus on professional networking and career development. Online identity on LinkedIn is shaped by an individual's professional experience. This can include work experience, education, skills, recommendations, and professional achievements. It allows professionals to establish their expertise, connect with colleagues, and showcase their qualifications.
Online Communities and Forums
Though online communities and forums centered around specific interests or hobbies, individuals have the opportunity to participate in discussions, ask questions, and share knowledge. Online identity within these communities is built based on the content contributed, expertise demonstrated, and the respect gained from other community members.
E-commerce and Online Shopping
When engaging in online shopping, individuals create accounts and profiles on e-commerce platforms. Online identity in this context involves personal information, purchase history, reviews, and ratings given to products or sellers. It influences the trustworthiness and credibility of an individual as a buyer or seller.
In each of these contexts, online identity is constructed through the information individuals share, their online activities, and the interactions they have with others. It plays a role in shaping how others perceive them and how they navigate various online spaces.
The Benefits of Having an Online Identity
Because the wide majority of the world has already adopted modern technology, having an online identity has become a necessity. However, there are a multitude of benefits which come with having an online identity, namely:
- Expanded Reach and Influence
- Professional Opportunities
- Networking and Collaboration
- Personal Branding
- Access to Resources and Information
Expanded Reach and Influence
Having an online identity allows individuals to extend their reach beyond physical boundaries. It provides a platform to share ideas, expertise, and creativity with a global audience. And this may potentially lead to increased influence and impact.
Professional Opportunities
An online identity can open doors to various professional opportunities. It allows individuals to showcase their skills, accomplishments, and qualifications to potential employers, clients, or collaborators. It acts as a digital resume, making it easier for others to discover and connect with them.
Networking and Collaboration
An online identity facilitates networking and collaboration by connecting individuals with like-minded people, professionals in their field, or communities of interest. It provides a platform to engage in meaningful discussions, share knowledge, and collaborate on projects, fostering valuable connections and relationships.
Personal Branding
Online identity enables individuals to shape and manage their personal brand effectively. They can curate their online presence to reflect their values, expertise, and unique qualities. This branding can help individuals stand out, establish credibility, and create a positive perception among peers, potential clients, or collaborators.
Access to Resources and Information
Having an online identity grants individuals access to a vast array of resources, information, and opportunities available on the internet. It allows them to tap into online communities, educational platforms, industry-specific websites, and research databases. This empowers them to stay informed, learn, and grow in their personal and professional pursuits.
Online Identity Risks and Challenges
As with any innovation, having an online identity does not come without risks. It’s important for people to be aware of these negative aspects and to take precautions to avoid becoming victims. Even more, it’s equally important to spread awareness and educate as many people as possible about these matters.
If proper security measures would be in place, the following situations could be prevented:
- Identity Theft
- Phishing and Social Engineering
- Online Reputation Damage
- Data Breaches and Privacy Breaches
Identity Theft
Online identity theft occurs when someone gains unauthorized access to personal information and uses it for fraudulent purposes. For example, a hacker might gain access to an individual's online banking account and use their identity to make unauthorized transactions or steal funds.
Phishing and Social Engineering
Phishing is a tactic used by cybercriminals to deceive individuals into sharing sensitive information such as passwords or credit card details by disguising themselves as a trustworthy entity. For example, a person may receive an email appearing to be from their bank, asking them to click on a link and provide login credentials. Hackers may use these credentials to gain unauthorized access to the victim's accounts.
Online Reputation Damage
In the digital age, a person's online reputation can have significant consequences. Negative or inappropriate content shared online, whether by oneself or others, can harm one's personal or professional reputation. For instance, a controversial tweet or a compromising photo shared online without consent can damage an individual's reputation and have long-lasting consequences.
Data Breaches and Privacy Breaches
Data breaches occur when sensitive information is accessed, stolen, or exposed due to security vulnerabilities in online systems. This can lead to the compromise of personal information, such as names, addresses, social security numbers, or financial data. An example is when a major retail company experiences a breach, resulting in the theft of customer credit card information from their database.
These risks and challenges highlight the importance of maintaining strong online security practices, being cautious with personal information sharing, and being vigilant about potential threats to online identity.
How ESelfKey May Improve your Online Identity Management
As online identities have become an integral part of daily life, it is crucial to prioritize privacy and security. Insufficient security measures or a lack of awareness regarding online safety can have long-lasting consequences for unsuspecting individuals.
Given this, ESelfKey aims to contribute to a safer digital future through the development of decentralized solutions. Decentralization has the potential to address numerous issues related to poor security in centralized systems.
One decentralized solution which ESelfKey proposes, and which may prevent data breaches in the future is ESelfKey iD.
ESelfKey iD
Designed with privacy and security in mind, ESelfKey iD may be the best solution for online identity management. Individuals who operate in the online world may be in charge of their private data, and this may prevent identity theft.
Because ESelfKey iD uses AI-Powered Proof of Individuality, unlawful access to a user’s private account may become considerably challenging. Artificial Intelligence is capable of detecting AI-generated images which bad players may use to try and compromise one’s online account.
And, with recurring selfie checks, ESelfKey iD aims to add an extra layer of security by continuously making sure that the user is who they claim to be. This way, security is enhanced and access to one’s private account is limited only to the user.
The goal is to enable individuals to operate in the online world confidently, so that people may enjoy the benefits of modern technology in a secure and safe manner.
Conclusions
The advent of modern technology has presented us with abundant opportunities for personal growth and advancement.
Utilizing online platforms and leveraging AI-powered tools offer numerous benefits in our day-to-day lives. Having an online identity has revolutionized the way we navigate challenges that were once formidable obstacles, such as remote work, distance learning, and long-distance communication.
To continue harnessing the potential of these remarkable opportunities, it is crucial that we take the necessary precautions to safeguard our online identities. The first step is to be well-informed and actively share knowledge and spread awareness.
ESelfKey strives to compile as much relevant information regarding digital identities, online identities, as well as privacy and security news in its blog. The more informed you are, the better the chances to prevent online security risks.
By prioritizing digital security, ESelfKey strives to empower individuals to embrace technology without sacrificing the safety of their digital identity.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Because of the increasing popularity of digital spaces, people have slowly started to migrate towards cyberspace.
It’s no longer uncommon for people to have an online presence, regardless of age, gender, or social status. We now have digital identities, digital meeting rooms, digital jobs, and digital entertainment. As long as there is access to the internet and people have the necessary gadgets, they will most certainly aim to create an online presence for themselves.
Cyberspace, also known as the metaverse, is like a parallel universe of our physical world, but with additional advantages: speed, efficiency, and flexibility. And, even though at the moment it has not reached its full potential, cyberspace can open doors to countless opportunities for knowledge and growth.
In spite of these amazing benefits, though, we must wonder: how well do we truly understand the concept of metaverse and the risks associated with it?
Cyberspace is a place filled with challenges as much as it is filled with potential and benefits. And, as individuals aiming to be part of such a complex and immersive digital space, it’s vital that we continuously educate ourselves on this topic.
This article strives to encompass as much vital information as possible about the fascinating world of metaverse, with all the good and the bad. Additionally, we will elaborate on SelfKey’s proposed decentralized solutions which aim to ensure the privacy and security of your digital identity as you operate in the online world.
Highlights
- An Introduction to Metaverse
- The Benefits of Metaverse
- The Dark Side of Metaverse
- How ESelfKey May Improve your Metaverse Experience
- Conclusions
An introduction to Metaverse
Metaverse and humanity
In order to operate in the digital space, individuals have to exist in. Therefore, the introduction of digital identities was something which came naturally with people’s need to belong on the internet.
Almost every person has had an online account, somewhere, or has been listed in some digital system. This was done either by the user themselves, or by other individuals in order to keep track of records more easily. The digital realm, therefore, has become an integral part of our daily lives, and it is something which almost every person seeks.
Even more, advancements in modern technology have unveiled the exciting possibility of interacting with virtual objects and spaces. Venturing into the metaverse has the potential to unlock doors to new realms of knowledge. It may ignite the imagination and provide opportunities to explore aspects of the world that may otherwise be physically out of reach.
All in all, the metaverse may change the way we, as society, interact and educate ourselves. With all of this in mind, ESelfKey strives to develop digital identity solutions that may enhance security and privacy as individuals begin to explore cyberspace.
Metaverse in a nutshell
The metaverse is a concept that came to be at the intersection of enhanced physical reality and persistent virtual space. It is centered around shared virtual spaces, consisting of various digital worlds, augmented reality, and the internet.
In simple terms, the metaverse represents a digital universe created and sustained by software, which is accessible through the internet. Within this virtual domain, individuals can interact with each other, as well as their virtual surroundings, in real-time.
For many years, the metaverse existed only as a theoretical concept, residing in the realm of people's imaginations. However, with the continuous advancements in technology, particularly in virtual and augmented reality, cyberspace is gradually capturing widespread attention. Although it is currently limited in scope, it has the potential to encompass endless possibilities in the future.
Depending on the context, cyberspace can serve as a parallel existence alongside the physical world, or it can strive to provide a fully immersive virtual environment. This leaves room for many opportunities for individuals to explore and share knowledge in the metaverse.
The Benefits of Metaverse
At its core, the metaverse has tremendous potential to revolutionize various aspects of society.
Due to its capacity to serve as a versatile platform for a wide range of applications, it may completely revolutionize the way we work, study, and socialize. It could facilitate many activities, such as virtual reality gaming, education, business meetings, social networking, and even virtual tourism.
Another notable feature of the metaverse is the possibility for users to create and design avatars. This aligns with SelfKey’s idea of customizable avatars, which may enable individuals to design avatars in any ways they please.
These avatars may enable interaction with other individuals or virtual objects in the metaverse. Furthermore, they may facilitate the creation of digital spaces that can be used for various purposes, such as virtual stores, events, and even entire cities.
The development and adoption of the metaverse may offer many potential benefits, such as:
- Improved Connectivity
- Digital Tourism
- Increased Accessibility
- Virtual Education
- New Experiences and Entertainment
- Streamlined Efficiency
Below, we will further elaborate on these advantages.
Improved Connectivity
Cyberspace allows for real-time communication and collaboration between individuals from anywhere around the world. Because physical distance is no longer an issue, individuals are able to build connections and easily collaborate on projects.
Digital Tourism
The metaverse may offer amazing opportunities for people to engage in virtual tourism. This means that individuals may delve into virtual recreations of amazing locations from the real, physical world. Additionally, they may be able to experience completely new, fascinating fictional realms which they’ve always dreamt of.
Increased Accessibility
Through the power of digital tools and endless creativity, the metaverse may become accessible from anywhere around the world. As long as there are stable internet connections, and with the proper devices, anyone could be part of this immersive experience.
This feature is particularly important, as it may facilitate participation for individuals with disabilities or mobility constraints.
Virtual Education
The internet has provided access to information which surely must’ve made learning much more accessible than ever before. However, cyberspace can bring education to the next level by allowing the creation of immersive, virtual classrooms.
Even more, individuals may be able to build realistic, interactive learning environments. This could prove to be incredibly helpful in terms of accessibility and education for young people all around the world.
New Experiences and Entertainment
By utilizing the potential of cyberspace, individuals may be able to experience unique scenarios and activities which may not be practical or possible in the physical world. For instance, they could participate in fantasy-based virtual reality games and simulations.
Streamlined Efficiency
The metaverse holds potential to streamline and enhance various business and organizational processes. This includes anything from meetings, training, and customer service, and it could facilitate debugging and solving particular technical issues much faster.
All in all, cyberspace represents a transformative landscape with far-reaching implications. It could potentially reshape the way we interact, learn, and engage with the world around us, and beyond. In spite of all these wonderful benefits, though, there are downsides to the metaverse which are worth mentioning.
The Dark Side of Metaverse
As stated above, cyberspace holds immense potential and possibilities. However, alongside these exciting prospects, it is crucial to acknowledge the challenges which come with this cutting-edge technology.
While the metaverse indeed raises concerns about health and social isolation, among other crucial factors, we will narrow our discussion to two primary aspects:
- Privacy Issues
- Identity Theft and Hacking
Privacy Issues
The metaverse relies on the utilization of Virtual Reality (VR) technology, which, like any cutting-edge innovation, presents its own set of challenges. As an extension of the internet, cyberspace confronts similar digital privacy and security issues, but perhaps at a more concerning level.
VR systems may collect user data, encompassing personal information and behavioral data, with the intention of enhancing the user experience. However, the collection and handling of such data carry inherent risks, including the potential for privacy breaches or unauthorized access.
Moreover, when engaging with VR applications and services developed by third parties, users should be aware that these entities may gather personal data for their own purposes, raising further privacy considerations.
Safeguarding this data is of utmost importance, as mishandling could expose individuals to privacy breaches, compromising their personal information and leaving them susceptible to identity theft or misuse.
Identity Theft and Hacking
The utilization of VR within the metaverse presents a vulnerable target for identity theft. With the aid of various machine learning algorithms, it may be relatively easy to manipulate sounds and visuals to a degree where they appear genuine.
Furthermore, attackers can exploit virtual reality platforms by introducing deceptive features aimed at extracting personal information from users. This susceptibility, similar to augmented reality, opens the door to ransomware attacks, where hackers compromise platforms and then demand a ransom.
Machine learning technologies also facilitate the manipulation of voices and videos while preserving their realism. If a hacker manages to access motion detection data from a VR headset, they could potentially employ it to generate a digital replica, commonly known as a deepfake.
A deepfake could then be used by malicious players to impersonate a user, or to try and access private accounts and systems in their name. While that is indeed a terrifying scenario, there are several decentralized solutions which may prevent such disasters.
How ESelfKey May Improve your Metaverse Experience
Given the multitude of benefits cyberspace offers, it comes as no surprise that malicious actors seek to exploit vulnerabilities within it.
With these facts in mind, ESelfKey proposes several decentralized solutions which may enhance security and prevent identity theft and other privacy concerns. These methods put a strong emphasis on privacy and security. The end goal is to empower individuals to confidently navigate the digital world.
ESelfKey iD
An innovative online identity verification method, ESelfKey iD was designed with the aim to safeguard user privacy and security. By utilizing ZK filters and AI-Powered Proof of Individuality, it strives to prevent unauthorized access to personal online accounts and systems by bots or identity thieves.
The purpose of ZK filters is to limit the amount of personal information shared when individuals interact with and engage with other individuals in digital spaces. If the shared data is limited, it may be insufficient for bad players to compromise. And this may enhance overall security and privacy.
AI-Powered Proof of Individuality is utilized with the aim to deter identity thieves from accessing a user’s online accounts with the latter’s stolen digital information. Thanks to AI’s ability to detect duplicates or fake, AI-generated images, ESelfKey iD may be able to combat and prevent these attempts.
This way, individuals may be able to enjoy the wonders of metaverse with confidence. Even more, they may ensure the privacy and security of their online persona.
SelfKey's Customizable NFTs
In the pursuit of a safer and decentralized future, ESelfKey recognizes the importance of individuality. To this end, ESelfKey may offer the means for individuals to embrace their uniqueness and make a mark in the metaverse through customization.
Through ESelfKey's Customizable NFTs, also known as Normies, users can attach these digital assets to their ESelfKey iD. And this may allow them to express their originality and gain access to exclusive features.
Normies are composed of Base NFTs and Wearables, offering users countless combinations and possibilities for customization. This provides users with an ideal opportunity to create digital representations that truly reflect their own identities.
SelfKey's ENS subdomains
Last, but not least, SelfKey's ENS subdomains strive to offer equal opportunities for individuals to own and personalize their domains.
The cost-effectiveness of these subdomains aims to make them affordable for everyone. And to possibly ensure that each person has the opportunity to be the owner of their own digital presence.
By implementing these online identity security solutions, and aiming to create a secure digital environment, ESelfKey is striving to contribute to a much safer digital future. The potential of cyberspace and modern technology is immense, and it’s worth being used for the good of the people.
Conclusions
Every day, technology reaches new heights, unlocking doors to unimaginable opportunities. However, like any innovation, there are those who will exploit it for their own gain, regardless of the harm caused.
Fortunately, with the right tools and knowledge, we may be able to prevent such occurrences.
The metaverse holds the power to revolutionize society and provide virtual access to knowledge like never before. But, it is essential to be aware of the accompanying risks. This way, we may navigate these remarkable digital realms safely.
SelfKey’s primary focus revolves around security and privacy. And every individual deserves these fundamental rights. People shouldn't have to risk their privacy and security in the pursuit of convenience or the use of modern-day technology.
By prioritizing security and privacy, ESelfKey strives to empower individuals to embrace technology without sacrificing the safety of their digital identity.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>The concept of digital identity has been adopted worldwide as a means for people to present themselves and operate in the online space.
Whether it’s for work, studying, or simply communicating, individuals are able to engage with one another from any corner of the world. But, because of the elusive nature of the internet, it’s difficult to tell whether an individual is who they claim to be.
This could make engaging with others in the online space rather challenging, even if they are verified. Users may unintentionally share their private information with bad players who could use them for personal gain. Malicious individuals may get access to services or carry out illegal activities in the victim’s name.
Even more, identity fraud or fake, AI-generated digital identities could influence polls and the decision-making process of a system. All of this could lead to devastating consequences for those whose digital identity has been compromised.
To prevent this, ESelfKey proposes the following online identity verification solutions: ESelfKey iD and Credential Locking, or proof of humanity locking.
ESelfKey iD is an innovative online identity verification method which may provide several benefits compared to traditional KYC checks. The process may be less costly, safer and more secure, so that every individual can benefit from its advantages.
This article will be focusing on how ESelfKey iD and credential locking may provide a more accessible means for individuals to authenticate themselves online from all over the world. Through this method, and with privacy and security in mind, ESelfKey is aiming to contribute to the development of a safer, decentralized future.
Highlights
- The Importance of Digital Identity Security
- SelfKey’s Proposed Online Identity Verification Solutions
- ESelfKey iD and Credential Locking: How it works
- The Benefits of ESelfKey iD and Credential Locking
- Conclusions
The Importance of Digital Identity Security
Why the safety of digital identity is crucial
Similar to our physical identities, our digital identities encompass all the information that describe us as individuals, such as: name, birth dates, full addresses, social security numbers, personally identifiable information (PII), or personal health information (PHI).
Nowadays, digital identities have become an integral part of our lives. From social media accounts to online banking, we rely on digital identities to conduct our daily activities. Thanks to the speed and efficiency of the internet, we are able to do these activities at a much faster pace.
However, with the convenience of digital identities comes the risk of identity theft, which can have severe consequences for individuals and organizations alike. Digital identities can be compromised at any moment, either by:
- cyberattacks which lead to data breaches, or
- accidentally clicking on a link messaged by a friend or family.
Browsing the internet from the comfort of our own homes may give us the illusion of safety. However, the theft of our digital identities is as alarming as having our physical wallets, with all of our personal documents inside, stolen.
Let us explore some of the negative impacts identity theft can leave us with.
The consequences of identity theft
Identity theft occurs when someone steals another person's personal information, such as their name, address, social security number, or financial details, with the intention of using it for fraudulent purposes.
The consequences of identity theft can be devastating for the victim, including financial losses, damaged credit scores, and reputational harm.
Moreover, bad players can use stolen digital identities for a wide range of criminal activities. For instance: accessing sensitive information, opening fraudulent bank accounts, and committing tax fraud. These activities can have severe outcomes for the victim and even lead to legal consequences for the perpetrator.
The dangers of sharing private information online
Sharing private information with unknown individuals is also a significant danger when it comes to digital identities.
Cybercriminals often use social engineering tactics to trick individuals into sharing their personal information. Some methods include phishing emails or fake websites. Once they obtain this information, they can use it to commit identity theft or other fraudulent activities.
This leads us to a serious concern that individuals all around the world are facing nowadays: a lack of proper security measures.
What can be done, then?
Identity theft and fraud are becoming more common in the digital world, and many individuals struggle to confidently operate online.
Despite privacy and security being fundamental human rights, most centralized systems still lack adequate security measures. Ideally, a decentralized environment where individuals can exercise their Self Sovereign Identity rights would help prevent data theft. By giving individuals ownership of their private information, cyberattacks would be less likely to succeed.
Given this, SelfKey recognizes the importance of developing decentralized solutions that may allow individuals to operate safely in the digital world. Below, we will thoroughly touch upon ESelfKey’s proposed solutions.
SelfKey’s Proposed Online Identity Verification Solutions
ESelfKey iD is an innovative and cost-effective online identity verification method designed to be more accessible than traditional KYC checks. The lack of recurring fees makes it accessible to every individual who wishes to authenticate themselves online.
ESelfKey iD uses the power of artificial intelligence (AI) in its online verification process, providing an extra layer of security. In addition to AI-powered verification, ESelfKey iD offers credential locking as a possible solution that may prevent identity fraud and access by fake, AI-generated digital identities.
All in all, with its focus on security, accessibility, and innovation, ESelfKey iD may become a leading solution for online identity verification.
ESelfKey iD and Credential Locking: How it works
ESelfKey aims to develop a simple and quick online identity verification method. That is why ESelfKey ID is meant to be not only cost-effective, but also user-friendly. This way, individuals may find it more accessible and easy to use.
Credential Locking, or proof of humanity, is a digital identity verification method used to establish that an individual is unique and real. It is used as part of the online identity verification process to confirm that an individual is not a bot, a fake account, or an identity thief.
The process
In the context of ESelfKey iD, Credential Locking may be used as an additional security measure for online identity verification. The following steps may be required:
- Users must provide a selfie during the initial KYC process.
- To access ESelfKey services, users are required to go through additional selfie checks. Their selfies will be compared to the original one taken during the KYC process.
- If the selfies match, users will be granted a Credential that can be locked with KEY. This verification process ensures that users' identities are authenticated and that they have a secure digital identity.
By locking KEY on their Credential, users contribute to the security of the ESelfKey ecosystem.
How will this provide security on the web?
SelfKey's Credential Locking method may not only provide a secure identity verification process but it may also offer several additional benefits to users. For instance:
- By locking their credentials, users may access exclusive features and services within the ESelfKey ecosystem. This means that users who have locked their credentials may have a higher level of trust and reputation within the network. This may allow them to benefit from additional functionalities that are not available to all users.
- Moreover, locking credentials may also allow users to accrue SELF tokens as a sign of their reputation within the ESelfKey ecosystem. Users can mint SELF tokens only if they can prove their identity by providing a matching selfie during the verification process. This will maintain the security of users’ digital identity and ensure that the ESelfKey ecosystem remains robust and secure.
- Furthermore, users can only withdraw their original KEY tokens if they can provide a matching selfie during the withdrawal process. This may provide an additional layer of security and ensure that unauthorized users cannot access a user's tokens.
Why provide selfies?
The purpose of providing selfies for the actions stated above is to ensure the users’ digital safety by verifying that they truly are who they claim to be. KEY and SELF tokens can thus be withdrawn or minted only after the user will have been able to successfully verify their identity.
The goal is to create a system in which users won’t have to worry about identity thieves or fake, AI-generated images being used to compromise their digital assets. By providing selfies, users may ensure that their accounts are secure and their privacy is not violated. ESelfKey’s AI-powered proof of individuality method may be the ideal solution in achieving this goal.
The Credential Locking method, therefore, may provide a secure and reliable system for identity verification, which benefits both users and the ESelfKey ecosystem as a whole. By locking their credentials, users may:
- protect their digital identity.
- access exclusive features.
- contribute to the security of the ESelfKey network.
The part AI plays
To enhance security in its online identity verification solutions, ESelfKey uses AI-Powered Proof of Individuality to facilitate the selfie matching process.
AI may prove to be particularly advantageous in this context, as its precision allows for the detection of several crucial factors:
- an individual's liveness.
- identity forgery.
- fake, AI-generated images.
This ensures that the identity verification process is secure and reliable. And that's because AI technology is capable of detecting any fraudulent attempts to game the system. Additionally, it can make sure that the selfies provided during the verification process are authentic.
By using AI-Powered Proof of Individuality, ESelfKey may be able to provide a trustworthy and robust system for digital identity verification, which is critical in today's digital world.
The Benefits of ESelfKey iD Credential Locking
As stated above, digital identities have become a target for malicious players that seek to exploit others for personal gain. And, with the weak security in some centralized systems, it’s crucial that we look for alternatives.
Given this, ESelfKey's credential locking method may provide a robust, reliable, and decentralized method for identity verification. It may offer the level of security and privacy that is critical in today’s digital world. Individuals may benefit from peace of mind and ensure that their digital identities are protected from fraudulent activities.
Even more, unlawful access to one’s personal accounts may become very challenging due to the extra layer of protection added by AI. Simply providing a true, authentic selfie can achieve all of this.
Conclusions
The rise of data breaches and identity theft has highlighted the need for a trustless and secure environment for online interactions. Individuals need to have confidence in the systems they use to protect their personal information to ensure the security of their digital identities.
Unfortunately, centralized systems may fail to provide proper security measures, which often lead to data breaches involving identity theft.
With the use of ESelfKey iD Credential Locking, a much safer network may be available in the future. By locking their credentials, users may prevent identity theft and fraud. Not only that, but they may gain access to exclusive features and services within the ESelfKey ecosystem.
SelfKey's goal is to develop a secure and trustless environment for online interactions. And that is highly important nowadays, as we become more and more accustomed to operating in the digital world.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details. The term "staking" is used solely as it is described here and does not mean any investment or similar activities.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>