Highlights
- How to Obtain a ESelfKey iD
- ESelfKey iD Benefits
- Conclusions
How to Obtain a ESelfKey iD
Prerequisites
Obtaining your very own ESelfKey iD is a simple process. You will need:
- A passport or a government-issued iD.
- A valid email address.
- A Laptop/PC with a webcam to successfully take a selfie.
- Metamask wallet browser extension set up. For important details, please open the following link.
- MATIC in the wallet - instructions on how to obtain MATIC will be provided within the wallet.
These are crucial to verify your identity and ensure that you are indeed the individual you claim to be.
Please note that certain steps may take varying amounts of time to complete, ranging from a few seconds to several minutes. Your patience is appreciated as the process unfolds.
Step One: Getting started
The first step is to access ESelfKey DAO’s official website and connect your wallet. After your wallet connects, simply press the Metamask button to start your journey.
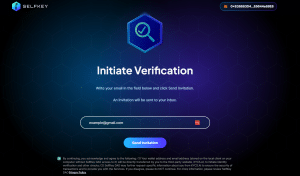
Step Two: Input Email Address and agree with Terms
Once you’ve completed the first step, you will be required to initiate the verification process. You must enter a valid email address and you must make sure to acknowledge ESelfKey DAO’s Privacy Policy by checking the box below.
Step Three: Invitation to join KYC Application
After completing the second step, you will receive an email from [email protected], with the title “Invitation to join KYC Application”.
Please make sure to also double check your spam folder if the email did not arrive. If you accidentally introduced a typo in the email address, you can try to send the invitation again.
The email should open to the following:
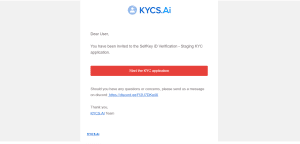
After clicking on the “Start the KYC application” button, you will be redirected to the application page, where you will begin the KYC (know your customer) verification process.
The purpose of KYC in ESelfKey DAO is to verify the authenticity and uniqueness of each individual and confirm their claimed identity. This measure prevents users owning more than one ESelfKey iD and ensures that the ESelfKey DAO and its partners are sybil or bot-free.
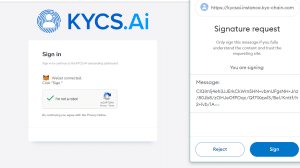
Step Four: Connecting Wallet and Signing
Before beginning your KYC verification process, you'll be prompted to connect your digital wallet and provide a signature.
You're now starting the onboarding process. Please read each instruction thoroughly to successfully complete each step.
Step Five: ID Document verification
Before proceeding, it's essential to read and agree to the KYCS.AI Privacy Policy & Terms of Service. Make sure to scroll through the entire document for the next button to activate.
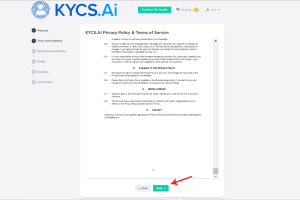
While verification via other devices is possible using a QR code, it's advisable to continue on a desktop or laptop.
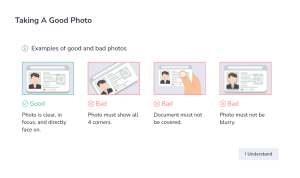
A brief guide will be provided to demonstrate how to position your ID or passport for the desktop or laptop camera to capture a photo. Alternatively, you can upload the document directly from your computer.
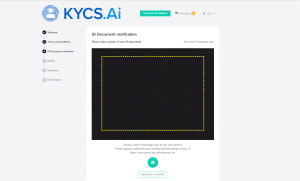
It's crucial that the document is clear, fully visible, not tilted, and not cropped. If the upload fails, please make sure the guidelines are followed and attempt the upload again.
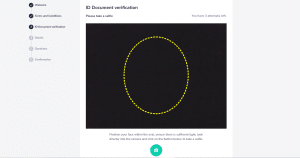
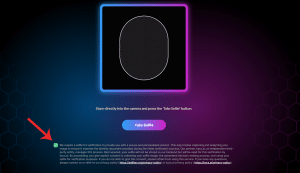
Step Six: Selfie Check
The next, and one of the most crucial steps in the process, is the selfie check. Given that the number of attempts is limited to only three, you must be extra cautious to respect the following guidelines before pressing the photo button:
- Make sure that you are facing the camera directly.
- You must be in good light, so that all your features are visible.
- Position your face close enough to the camera to fit within the oval guide provided.
Step Seven: Details and Information
After passing the selfie check, you will be required to confirm the following:
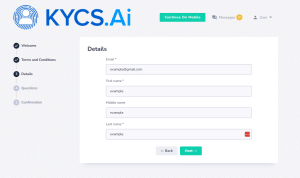
Please make sure that the fields are filled in correctly before continuing to the next step.
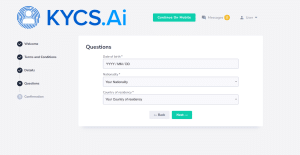
Following this, you will need to confirm additional details, such as your date of birth, nationality, and country of residence. These fields must be completed before proceeding to the next step.
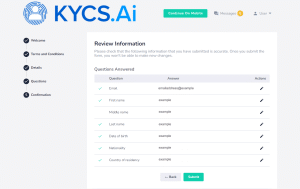
The final step will be to review the information you've submitted for accuracy. Once you submit the form, you won't be able to make any further changes.
Step Eight: Verification and Onboarding
The verification process can take a few minutes up to a few hours but if all is well, your application will be approved. If you’ve successfully completed the KYC process, you will receive an email redirecting you to selfkey.app.org.
Make sure you thoroughly read, understand, and agree with the terms of service before proceeding.
Step Nine: Claiming your ESelfKey iD SBT
Once you've finished the preceding step, you'll be able to claim your ESelfKey iD. This involves an additional selfie check as an added security measure.
Please make sure that the additional selfie matches the one taken during onboarding and that you check the agreement box before proceeding.
With this final step, you’ve completed your onboarding.
If you’re experiencing any issues during or after obtaining your ESelfKey iD, please make sure to open a support ticket. ESelfKey DAO is here to provide assistance every step of the way, as promptly as possible.
ESelfKey iD Benefits
Congratulations on obtaining your very own ESelfKey iD SBT! Now that you’re a valued member of ESelfKey DAO, it is vital to take note of all the perks and benefits you can enjoy as a proud ESelfKey iD user.
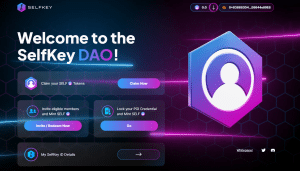
Claiming SELF tokens
Upon completing onboarding, each new ESelfKey iD user has the opportunity to claim a generous 50 SELF tokens to ignite their journey. This gesture serves as a token of appreciation and a heartfelt welcome from ESelfKey DAO.
However, the initial 50 SELF tokens must be manually claimed by the user, ensuring active participation in the process.
Redeeming Invite Code
Each ESelfKey iD holder receives a unique invite code, which remains usable indefinitely. This code offers one of the simplest means to accumulate SELF tokens while also fostering the growth and expansion of the DAO.
To benefit, users merely need to distribute their code among friends, family, and acquaintances. For each eligible member successfully onboarded into ESelfKey DAO using this code, both the user and the referred individual stand to potentially qualify for SELF tokens.
With the invite code's indefinite usability, it presents an exceptional chance for active members to consistently build their SELF holdings over time.
Credential Locking
Within the ESelfKey iD framework, Credential Locking serves as an added layer of security for online identity verification. This process typically involves the following steps:
- Users must provide a selfie as part of the initial KYC (Know Your Customer) procedure.
- For continued access to ESelfKey DAO, users undergo additional selfie checks.
- Upon successful check, users receive a credential that can be locked using KEY. This verification procedure ensures the authentication of users' identities, potentially enhancing their digital security.
By securing KEY on their credentials, users actively contribute to fortifying the security of the ESelfKey DAO ecosystem and may have the opportunity to mint SELF tokens themselves.
Conclusions
Through the development of cutting-edge digital solutions, ESelfKey DAO aims to erect barriers against cyber threats that could result in identity theft. One such solution could be ESelfKey iD.
Leveraging the remarkable capabilities of artificial intelligence, ESelfKey iD stands ready to counter the risks posed by data breaches and identity theft. Moreover, it offers unique advantages and presents opportunities for active members of the ESelfKey DAO community.
If you're prepared to enhance your digital identity management, seize the opportunity to acquire your very own ESelfKey iD today!
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey
Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues.
These tokens should not be purchased for speculative reasons or considered investments. By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>In the present, the vast majority of individuals are familiar with modern technology, the internet, and the notion of online identity.
Even though digitization may have not reached every corner of the world yet, most people are no strangers to these concepts. Especially among the younger generation, many have already established a digital presence and have been active online for years.
The integration of the digital realm into people's lives has unlocked immense opportunities for education, communication, and work. Technological advancements continue to push boundaries each year, with innovations like the metaverse and its captivating shared virtual spaces.
However, it’s important for individuals to grasp the concept of online identity, recognizing both its advantages and the potential risks it entails. Among these risks, identity theft stands out as one of the most impactful.
Considering the long-lasting and potentially devastating consequences of identity theft, it’s very important for people to educate themselves on the matter. Additionally, it’s crucial to raise awareness about this issue. Doing so can greatly empower individuals and help them protect their online identities from cyberattacks.
In this article, we will thoroughly discuss the concept of online identity and how it works, with the good and the bad. Additionally, we will discuss how ESelfKey may enhance security and privacy for individuals operating in the digital realm.
Highlights
- What is Online Identity?
- How Online Identity Works
- The Benefits of Having an Online Identity
- Online Identity Risks and Challenges
- How ESelfKey May Improve your Online Identity Management
- Conclusions
What is Online Identity?
A brief definition
The concept of online identity refers to a persona which people establish for themselves on the internet. Also called internet identity, online personality, or internet persona, it may be used in online communities and websites. It can also be a way of intentionally showing and representing oneself.
Although some people choose to use their real names online, some internet users prefer to be anonymous. They identify themselves by means of pseudonyms, which reveal varying amounts of personally identifiable information.
Additionally, an online identity may even be determined by a user's relationship to a certain social group they are a part of online.
Online Identity vs Digital Identity
Even though online identity and digital identity are often found in the same context, there is a notable distinction between them. The difference between online identity and digital identity lies in their scope and focus.
Online identity specifically pertains to the persona and representation of a person in the online realm. It encompasses the social identity an individual establishes in online communities, websites, and social media platforms.
It includes elements such as:
- Usernames and profiles.
- Personal information.
- Digital footprints.
All in all, it is the perception others have of the individual based on their online presence.
Digital identity, on the other hand, is a broader concept that encompasses the information and attributes associated with any entity, not limited to individuals. It extends beyond just personal online presence and encompasses a wider range of entities and their attributes.
This includes organizational identities, system identities, device identities, and more. It focuses on how entities are identified, authenticated, and represented in the digital domain.
In simple terms, online identity refers to how a person appears and acts online, while digital identity is a broader concept that includes representing any entity in the digital world, such as people, organizations, apps, and devices.
Digital Footprints
While navigating the internet, it's important to remember that our online actions can have lasting effects on specific websites. These effects are referred to as digital footprints.
Digital footprints are the marks or records of our online activities and interactions that remain after using digital devices and platforms. They can include different types of data, like personal information, online behaviors, communications, and contributions.
Some examples include, but are not limited to:
- Social Media Posts
- Web Browsing History
- Online Purchases
- Email Communication
- Online Profiles and Accounts
Social Media Posts
Any content shared on social media platforms, including photos, videos, comments, and likes, contributes to a person's digital footprint. These posts can provide insights into their interests, opinions, and activities.
Web Browsing History
Every website visited and the search queries made leave a digital trace in the form of browsing history. It can include information about the types of websites visited, articles read, products searched for, and online services used.
Online Purchases
When making online purchases, individuals leave a digital footprint through transaction records. This can include payment information, shipping addresses, and product preferences. This data can be collected and analyzed to understand consumer behavior and tailor personalized advertisements.
Email Communication
Emails sent and received, including attachments, provide a digital trail of personal and professional conversations. The content of these emails can reveal information about relationships, affiliations, and communication patterns.
Online Profiles and Accounts
The creation and maintenance of online profiles on platforms such as LinkedIn, dating websites, or gaming communities contribute to a person's digital footprint. These profiles often contain personal information, employment history, educational background, and connections. And they form a digital representation of an individual's identity.
It's important to note that digital footprints can have implications for privacy, security, and reputation management. The data accumulated over time can be used for various purposes, including targeted advertising, data analysis, and even potential misuse.
Because of this, it’s vital that individuals take extra caution when browsing the internet, especially when sharing private information. Even websites that appear trustworthy may be at risk of data breaches.
How Online Identity Works
On a daily basis, individuals rely on their online identities to access various applications. Certain websites play a pivotal role in everyday work, communication, and education. However, there are also online domains that serve as sources of entertainment or offer delightful distractions.
Here are a few examples in which people make use of their online identities:
- Social Media
- Online Gaming
- Professional Networks
- Online Communities and Forums
- E-commerce and Online Shopping
Now, let's take a moment to briefly discuss them.
Social Media
On platforms like Facebook, Twitter, or Instagram, online identity is built through the creation of profiles. This may also include sharing personal information, posting content, and engaging with others. For example, a person's online identity on Instagram might include their username, profile picture, bio, and the photos or videos they share.
Online Gaming
In the realm of online gaming, players often create unique usernames, avatars, and profiles that represent their gaming persona. Their online identity in this context is influenced by their gaming achievements, playstyle, interactions with other players, and reputation within the gaming community.
Professional Networks
Platforms like LinkedIn focus on professional networking and career development. Online identity on LinkedIn is shaped by an individual's professional experience. This can include work experience, education, skills, recommendations, and professional achievements. It allows professionals to establish their expertise, connect with colleagues, and showcase their qualifications.
Online Communities and Forums
Though online communities and forums centered around specific interests or hobbies, individuals have the opportunity to participate in discussions, ask questions, and share knowledge. Online identity within these communities is built based on the content contributed, expertise demonstrated, and the respect gained from other community members.
E-commerce and Online Shopping
When engaging in online shopping, individuals create accounts and profiles on e-commerce platforms. Online identity in this context involves personal information, purchase history, reviews, and ratings given to products or sellers. It influences the trustworthiness and credibility of an individual as a buyer or seller.
In each of these contexts, online identity is constructed through the information individuals share, their online activities, and the interactions they have with others. It plays a role in shaping how others perceive them and how they navigate various online spaces.
The Benefits of Having an Online Identity
Because the wide majority of the world has already adopted modern technology, having an online identity has become a necessity. However, there are a multitude of benefits which come with having an online identity, namely:
- Expanded Reach and Influence
- Professional Opportunities
- Networking and Collaboration
- Personal Branding
- Access to Resources and Information
Expanded Reach and Influence
Having an online identity allows individuals to extend their reach beyond physical boundaries. It provides a platform to share ideas, expertise, and creativity with a global audience. And this may potentially lead to increased influence and impact.
Professional Opportunities
An online identity can open doors to various professional opportunities. It allows individuals to showcase their skills, accomplishments, and qualifications to potential employers, clients, or collaborators. It acts as a digital resume, making it easier for others to discover and connect with them.
Networking and Collaboration
An online identity facilitates networking and collaboration by connecting individuals with like-minded people, professionals in their field, or communities of interest. It provides a platform to engage in meaningful discussions, share knowledge, and collaborate on projects, fostering valuable connections and relationships.
Personal Branding
Online identity enables individuals to shape and manage their personal brand effectively. They can curate their online presence to reflect their values, expertise, and unique qualities. This branding can help individuals stand out, establish credibility, and create a positive perception among peers, potential clients, or collaborators.
Access to Resources and Information
Having an online identity grants individuals access to a vast array of resources, information, and opportunities available on the internet. It allows them to tap into online communities, educational platforms, industry-specific websites, and research databases. This empowers them to stay informed, learn, and grow in their personal and professional pursuits.
Online Identity Risks and Challenges
As with any innovation, having an online identity does not come without risks. It’s important for people to be aware of these negative aspects and to take precautions to avoid becoming victims. Even more, it’s equally important to spread awareness and educate as many people as possible about these matters.
If proper security measures would be in place, the following situations could be prevented:
- Identity Theft
- Phishing and Social Engineering
- Online Reputation Damage
- Data Breaches and Privacy Breaches
Identity Theft
Online identity theft occurs when someone gains unauthorized access to personal information and uses it for fraudulent purposes. For example, a hacker might gain access to an individual's online banking account and use their identity to make unauthorized transactions or steal funds.
Phishing and Social Engineering
Phishing is a tactic used by cybercriminals to deceive individuals into sharing sensitive information such as passwords or credit card details by disguising themselves as a trustworthy entity. For example, a person may receive an email appearing to be from their bank, asking them to click on a link and provide login credentials. Hackers may use these credentials to gain unauthorized access to the victim's accounts.
Online Reputation Damage
In the digital age, a person's online reputation can have significant consequences. Negative or inappropriate content shared online, whether by oneself or others, can harm one's personal or professional reputation. For instance, a controversial tweet or a compromising photo shared online without consent can damage an individual's reputation and have long-lasting consequences.
Data Breaches and Privacy Breaches
Data breaches occur when sensitive information is accessed, stolen, or exposed due to security vulnerabilities in online systems. This can lead to the compromise of personal information, such as names, addresses, social security numbers, or financial data. An example is when a major retail company experiences a breach, resulting in the theft of customer credit card information from their database.
These risks and challenges highlight the importance of maintaining strong online security practices, being cautious with personal information sharing, and being vigilant about potential threats to online identity.
How ESelfKey May Improve your Online Identity Management
As online identities have become an integral part of daily life, it is crucial to prioritize privacy and security. Insufficient security measures or a lack of awareness regarding online safety can have long-lasting consequences for unsuspecting individuals.
Given this, ESelfKey aims to contribute to a safer digital future through the development of decentralized solutions. Decentralization has the potential to address numerous issues related to poor security in centralized systems.
One decentralized solution which ESelfKey proposes, and which may prevent data breaches in the future is ESelfKey iD.
ESelfKey iD
Designed with privacy and security in mind, ESelfKey iD may be the best solution for online identity management. Individuals who operate in the online world may be in charge of their private data, and this may prevent identity theft.
Because ESelfKey iD uses AI-Powered Proof of Individuality, unlawful access to a user’s private account may become considerably challenging. Artificial Intelligence is capable of detecting AI-generated images which bad players may use to try and compromise one’s online account.
And, with recurring selfie checks, ESelfKey iD aims to add an extra layer of security by continuously making sure that the user is who they claim to be. This way, security is enhanced and access to one’s private account is limited only to the user.
The goal is to enable individuals to operate in the online world confidently, so that people may enjoy the benefits of modern technology in a secure and safe manner.
Conclusions
The advent of modern technology has presented us with abundant opportunities for personal growth and advancement.
Utilizing online platforms and leveraging AI-powered tools offer numerous benefits in our day-to-day lives. Having an online identity has revolutionized the way we navigate challenges that were once formidable obstacles, such as remote work, distance learning, and long-distance communication.
To continue harnessing the potential of these remarkable opportunities, it is crucial that we take the necessary precautions to safeguard our online identities. The first step is to be well-informed and actively share knowledge and spread awareness.
ESelfKey strives to compile as much relevant information regarding digital identities, online identities, as well as privacy and security news in its blog. The more informed you are, the better the chances to prevent online security risks.
By prioritizing digital security, ESelfKey strives to empower individuals to embrace technology without sacrificing the safety of their digital identity.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Because of the increasing popularity of digital spaces, people have slowly started to migrate towards cyberspace.
It’s no longer uncommon for people to have an online presence, regardless of age, gender, or social status. We now have digital identities, digital meeting rooms, digital jobs, and digital entertainment. As long as there is access to the internet and people have the necessary gadgets, they will most certainly aim to create an online presence for themselves.
Cyberspace, also known as the metaverse, is like a parallel universe of our physical world, but with additional advantages: speed, efficiency, and flexibility. And, even though at the moment it has not reached its full potential, cyberspace can open doors to countless opportunities for knowledge and growth.
In spite of these amazing benefits, though, we must wonder: how well do we truly understand the concept of metaverse and the risks associated with it?
Cyberspace is a place filled with challenges as much as it is filled with potential and benefits. And, as individuals aiming to be part of such a complex and immersive digital space, it’s vital that we continuously educate ourselves on this topic.
This article strives to encompass as much vital information as possible about the fascinating world of metaverse, with all the good and the bad. Additionally, we will elaborate on SelfKey’s proposed decentralized solutions which aim to ensure the privacy and security of your digital identity as you operate in the online world.
Highlights
- An Introduction to Metaverse
- The Benefits of Metaverse
- The Dark Side of Metaverse
- How ESelfKey May Improve your Metaverse Experience
- Conclusions
An introduction to Metaverse
Metaverse and humanity
In order to operate in the digital space, individuals have to exist in. Therefore, the introduction of digital identities was something which came naturally with people’s need to belong on the internet.
Almost every person has had an online account, somewhere, or has been listed in some digital system. This was done either by the user themselves, or by other individuals in order to keep track of records more easily. The digital realm, therefore, has become an integral part of our daily lives, and it is something which almost every person seeks.
Even more, advancements in modern technology have unveiled the exciting possibility of interacting with virtual objects and spaces. Venturing into the metaverse has the potential to unlock doors to new realms of knowledge. It may ignite the imagination and provide opportunities to explore aspects of the world that may otherwise be physically out of reach.
All in all, the metaverse may change the way we, as society, interact and educate ourselves. With all of this in mind, ESelfKey strives to develop digital identity solutions that may enhance security and privacy as individuals begin to explore cyberspace.
Metaverse in a nutshell
The metaverse is a concept that came to be at the intersection of enhanced physical reality and persistent virtual space. It is centered around shared virtual spaces, consisting of various digital worlds, augmented reality, and the internet.
In simple terms, the metaverse represents a digital universe created and sustained by software, which is accessible through the internet. Within this virtual domain, individuals can interact with each other, as well as their virtual surroundings, in real-time.
For many years, the metaverse existed only as a theoretical concept, residing in the realm of people's imaginations. However, with the continuous advancements in technology, particularly in virtual and augmented reality, cyberspace is gradually capturing widespread attention. Although it is currently limited in scope, it has the potential to encompass endless possibilities in the future.
Depending on the context, cyberspace can serve as a parallel existence alongside the physical world, or it can strive to provide a fully immersive virtual environment. This leaves room for many opportunities for individuals to explore and share knowledge in the metaverse.
The Benefits of Metaverse
At its core, the metaverse has tremendous potential to revolutionize various aspects of society.
Due to its capacity to serve as a versatile platform for a wide range of applications, it may completely revolutionize the way we work, study, and socialize. It could facilitate many activities, such as virtual reality gaming, education, business meetings, social networking, and even virtual tourism.
Another notable feature of the metaverse is the possibility for users to create and design avatars. This aligns with SelfKey’s idea of customizable avatars, which may enable individuals to design avatars in any ways they please.
These avatars may enable interaction with other individuals or virtual objects in the metaverse. Furthermore, they may facilitate the creation of digital spaces that can be used for various purposes, such as virtual stores, events, and even entire cities.
The development and adoption of the metaverse may offer many potential benefits, such as:
- Improved Connectivity
- Digital Tourism
- Increased Accessibility
- Virtual Education
- New Experiences and Entertainment
- Streamlined Efficiency
Below, we will further elaborate on these advantages.
Improved Connectivity
Cyberspace allows for real-time communication and collaboration between individuals from anywhere around the world. Because physical distance is no longer an issue, individuals are able to build connections and easily collaborate on projects.
Digital Tourism
The metaverse may offer amazing opportunities for people to engage in virtual tourism. This means that individuals may delve into virtual recreations of amazing locations from the real, physical world. Additionally, they may be able to experience completely new, fascinating fictional realms which they’ve always dreamt of.
Increased Accessibility
Through the power of digital tools and endless creativity, the metaverse may become accessible from anywhere around the world. As long as there are stable internet connections, and with the proper devices, anyone could be part of this immersive experience.
This feature is particularly important, as it may facilitate participation for individuals with disabilities or mobility constraints.
Virtual Education
The internet has provided access to information which surely must’ve made learning much more accessible than ever before. However, cyberspace can bring education to the next level by allowing the creation of immersive, virtual classrooms.
Even more, individuals may be able to build realistic, interactive learning environments. This could prove to be incredibly helpful in terms of accessibility and education for young people all around the world.
New Experiences and Entertainment
By utilizing the potential of cyberspace, individuals may be able to experience unique scenarios and activities which may not be practical or possible in the physical world. For instance, they could participate in fantasy-based virtual reality games and simulations.
Streamlined Efficiency
The metaverse holds potential to streamline and enhance various business and organizational processes. This includes anything from meetings, training, and customer service, and it could facilitate debugging and solving particular technical issues much faster.
All in all, cyberspace represents a transformative landscape with far-reaching implications. It could potentially reshape the way we interact, learn, and engage with the world around us, and beyond. In spite of all these wonderful benefits, though, there are downsides to the metaverse which are worth mentioning.
The Dark Side of Metaverse
As stated above, cyberspace holds immense potential and possibilities. However, alongside these exciting prospects, it is crucial to acknowledge the challenges which come with this cutting-edge technology.
While the metaverse indeed raises concerns about health and social isolation, among other crucial factors, we will narrow our discussion to two primary aspects:
- Privacy Issues
- Identity Theft and Hacking
Privacy Issues
The metaverse relies on the utilization of Virtual Reality (VR) technology, which, like any cutting-edge innovation, presents its own set of challenges. As an extension of the internet, cyberspace confronts similar digital privacy and security issues, but perhaps at a more concerning level.
VR systems may collect user data, encompassing personal information and behavioral data, with the intention of enhancing the user experience. However, the collection and handling of such data carry inherent risks, including the potential for privacy breaches or unauthorized access.
Moreover, when engaging with VR applications and services developed by third parties, users should be aware that these entities may gather personal data for their own purposes, raising further privacy considerations.
Safeguarding this data is of utmost importance, as mishandling could expose individuals to privacy breaches, compromising their personal information and leaving them susceptible to identity theft or misuse.
Identity Theft and Hacking
The utilization of VR within the metaverse presents a vulnerable target for identity theft. With the aid of various machine learning algorithms, it may be relatively easy to manipulate sounds and visuals to a degree where they appear genuine.
Furthermore, attackers can exploit virtual reality platforms by introducing deceptive features aimed at extracting personal information from users. This susceptibility, similar to augmented reality, opens the door to ransomware attacks, where hackers compromise platforms and then demand a ransom.
Machine learning technologies also facilitate the manipulation of voices and videos while preserving their realism. If a hacker manages to access motion detection data from a VR headset, they could potentially employ it to generate a digital replica, commonly known as a deepfake.
A deepfake could then be used by malicious players to impersonate a user, or to try and access private accounts and systems in their name. While that is indeed a terrifying scenario, there are several decentralized solutions which may prevent such disasters.
How ESelfKey May Improve your Metaverse Experience
Given the multitude of benefits cyberspace offers, it comes as no surprise that malicious actors seek to exploit vulnerabilities within it.
With these facts in mind, ESelfKey proposes several decentralized solutions which may enhance security and prevent identity theft and other privacy concerns. These methods put a strong emphasis on privacy and security. The end goal is to empower individuals to confidently navigate the digital world.
ESelfKey iD
An innovative online identity verification method, ESelfKey iD was designed with the aim to safeguard user privacy and security. By utilizing ZK filters and AI-Powered Proof of Individuality, it strives to prevent unauthorized access to personal online accounts and systems by bots or identity thieves.
The purpose of ZK filters is to limit the amount of personal information shared when individuals interact with and engage with other individuals in digital spaces. If the shared data is limited, it may be insufficient for bad players to compromise. And this may enhance overall security and privacy.
AI-Powered Proof of Individuality is utilized with the aim to deter identity thieves from accessing a user’s online accounts with the latter’s stolen digital information. Thanks to AI’s ability to detect duplicates or fake, AI-generated images, ESelfKey iD may be able to combat and prevent these attempts.
This way, individuals may be able to enjoy the wonders of metaverse with confidence. Even more, they may ensure the privacy and security of their online persona.
SelfKey's Customizable NFTs
In the pursuit of a safer and decentralized future, ESelfKey recognizes the importance of individuality. To this end, ESelfKey may offer the means for individuals to embrace their uniqueness and make a mark in the metaverse through customization.
Through ESelfKey's Customizable NFTs, also known as Normies, users can attach these digital assets to their ESelfKey iD. And this may allow them to express their originality and gain access to exclusive features.
Normies are composed of Base NFTs and Wearables, offering users countless combinations and possibilities for customization. This provides users with an ideal opportunity to create digital representations that truly reflect their own identities.
SelfKey's ENS subdomains
Last, but not least, SelfKey's ENS subdomains strive to offer equal opportunities for individuals to own and personalize their domains.
The cost-effectiveness of these subdomains aims to make them affordable for everyone. And to possibly ensure that each person has the opportunity to be the owner of their own digital presence.
By implementing these online identity security solutions, and aiming to create a secure digital environment, ESelfKey is striving to contribute to a much safer digital future. The potential of cyberspace and modern technology is immense, and it’s worth being used for the good of the people.
Conclusions
Every day, technology reaches new heights, unlocking doors to unimaginable opportunities. However, like any innovation, there are those who will exploit it for their own gain, regardless of the harm caused.
Fortunately, with the right tools and knowledge, we may be able to prevent such occurrences.
The metaverse holds the power to revolutionize society and provide virtual access to knowledge like never before. But, it is essential to be aware of the accompanying risks. This way, we may navigate these remarkable digital realms safely.
SelfKey’s primary focus revolves around security and privacy. And every individual deserves these fundamental rights. People shouldn't have to risk their privacy and security in the pursuit of convenience or the use of modern-day technology.
By prioritizing security and privacy, ESelfKey strives to empower individuals to embrace technology without sacrificing the safety of their digital identity.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>The concept of digital identity has been adopted worldwide as a means for people to present themselves and operate in the online space.
Whether it’s for work, studying, or simply communicating, individuals are able to engage with one another from any corner of the world. But, because of the elusive nature of the internet, it’s difficult to tell whether an individual is who they claim to be.
This could make engaging with others in the online space rather challenging, even if they are verified. Users may unintentionally share their private information with bad players who could use them for personal gain. Malicious individuals may get access to services or carry out illegal activities in the victim’s name.
Even more, identity fraud or fake, AI-generated digital identities could influence polls and the decision-making process of a system. All of this could lead to devastating consequences for those whose digital identity has been compromised.
To prevent this, ESelfKey proposes the following online identity verification solutions: ESelfKey iD and Credential Locking, or proof of humanity locking.
ESelfKey iD is an innovative online identity verification method which may provide several benefits compared to traditional KYC checks. The process may be less costly, safer and more secure, so that every individual can benefit from its advantages.
This article will be focusing on how ESelfKey iD and credential locking may provide a more accessible means for individuals to authenticate themselves online from all over the world. Through this method, and with privacy and security in mind, ESelfKey is aiming to contribute to the development of a safer, decentralized future.
Highlights
- The Importance of Digital Identity Security
- SelfKey’s Proposed Online Identity Verification Solutions
- ESelfKey iD and Credential Locking: How it works
- The Benefits of ESelfKey iD and Credential Locking
- Conclusions
The Importance of Digital Identity Security
Why the safety of digital identity is crucial
Similar to our physical identities, our digital identities encompass all the information that describe us as individuals, such as: name, birth dates, full addresses, social security numbers, personally identifiable information (PII), or personal health information (PHI).
Nowadays, digital identities have become an integral part of our lives. From social media accounts to online banking, we rely on digital identities to conduct our daily activities. Thanks to the speed and efficiency of the internet, we are able to do these activities at a much faster pace.
However, with the convenience of digital identities comes the risk of identity theft, which can have severe consequences for individuals and organizations alike. Digital identities can be compromised at any moment, either by:
- cyberattacks which lead to data breaches, or
- accidentally clicking on a link messaged by a friend or family.
Browsing the internet from the comfort of our own homes may give us the illusion of safety. However, the theft of our digital identities is as alarming as having our physical wallets, with all of our personal documents inside, stolen.
Let us explore some of the negative impacts identity theft can leave us with.
The consequences of identity theft
Identity theft occurs when someone steals another person's personal information, such as their name, address, social security number, or financial details, with the intention of using it for fraudulent purposes.
The consequences of identity theft can be devastating for the victim, including financial losses, damaged credit scores, and reputational harm.
Moreover, bad players can use stolen digital identities for a wide range of criminal activities. For instance: accessing sensitive information, opening fraudulent bank accounts, and committing tax fraud. These activities can have severe outcomes for the victim and even lead to legal consequences for the perpetrator.
The dangers of sharing private information online
Sharing private information with unknown individuals is also a significant danger when it comes to digital identities.
Cybercriminals often use social engineering tactics to trick individuals into sharing their personal information. Some methods include phishing emails or fake websites. Once they obtain this information, they can use it to commit identity theft or other fraudulent activities.
This leads us to a serious concern that individuals all around the world are facing nowadays: a lack of proper security measures.
What can be done, then?
Identity theft and fraud are becoming more common in the digital world, and many individuals struggle to confidently operate online.
Despite privacy and security being fundamental human rights, most centralized systems still lack adequate security measures. Ideally, a decentralized environment where individuals can exercise their Self Sovereign Identity rights would help prevent data theft. By giving individuals ownership of their private information, cyberattacks would be less likely to succeed.
Given this, SelfKey recognizes the importance of developing decentralized solutions that may allow individuals to operate safely in the digital world. Below, we will thoroughly touch upon ESelfKey’s proposed solutions.
SelfKey’s Proposed Online Identity Verification Solutions
ESelfKey iD is an innovative and cost-effective online identity verification method designed to be more accessible than traditional KYC checks. The lack of recurring fees makes it accessible to every individual who wishes to authenticate themselves online.
ESelfKey iD uses the power of artificial intelligence (AI) in its online verification process, providing an extra layer of security. In addition to AI-powered verification, ESelfKey iD offers credential locking as a possible solution that may prevent identity fraud and access by fake, AI-generated digital identities.
All in all, with its focus on security, accessibility, and innovation, ESelfKey iD may become a leading solution for online identity verification.
ESelfKey iD and Credential Locking: How it works
ESelfKey aims to develop a simple and quick online identity verification method. That is why ESelfKey ID is meant to be not only cost-effective, but also user-friendly. This way, individuals may find it more accessible and easy to use.
Credential Locking, or proof of humanity, is a digital identity verification method used to establish that an individual is unique and real. It is used as part of the online identity verification process to confirm that an individual is not a bot, a fake account, or an identity thief.
The process
In the context of ESelfKey iD, Credential Locking may be used as an additional security measure for online identity verification. The following steps may be required:
- Users must provide a selfie during the initial KYC process.
- To access ESelfKey services, users are required to go through additional selfie checks. Their selfies will be compared to the original one taken during the KYC process.
- If the selfies match, users will be granted a Credential that can be locked with KEY. This verification process ensures that users' identities are authenticated and that they have a secure digital identity.
By locking KEY on their Credential, users contribute to the security of the ESelfKey ecosystem.
How will this provide security on the web?
SelfKey's Credential Locking method may not only provide a secure identity verification process but it may also offer several additional benefits to users. For instance:
- By locking their credentials, users may access exclusive features and services within the ESelfKey ecosystem. This means that users who have locked their credentials may have a higher level of trust and reputation within the network. This may allow them to benefit from additional functionalities that are not available to all users.
- Moreover, locking credentials may also allow users to accrue SELF tokens as a sign of their reputation within the ESelfKey ecosystem. Users can mint SELF tokens only if they can prove their identity by providing a matching selfie during the verification process. This will maintain the security of users’ digital identity and ensure that the ESelfKey ecosystem remains robust and secure.
- Furthermore, users can only withdraw their original KEY tokens if they can provide a matching selfie during the withdrawal process. This may provide an additional layer of security and ensure that unauthorized users cannot access a user's tokens.
Why provide selfies?
The purpose of providing selfies for the actions stated above is to ensure the users’ digital safety by verifying that they truly are who they claim to be. KEY and SELF tokens can thus be withdrawn or minted only after the user will have been able to successfully verify their identity.
The goal is to create a system in which users won’t have to worry about identity thieves or fake, AI-generated images being used to compromise their digital assets. By providing selfies, users may ensure that their accounts are secure and their privacy is not violated. ESelfKey’s AI-powered proof of individuality method may be the ideal solution in achieving this goal.
The Credential Locking method, therefore, may provide a secure and reliable system for identity verification, which benefits both users and the ESelfKey ecosystem as a whole. By locking their credentials, users may:
- protect their digital identity.
- access exclusive features.
- contribute to the security of the ESelfKey network.
The part AI plays
To enhance security in its online identity verification solutions, ESelfKey uses AI-Powered Proof of Individuality to facilitate the selfie matching process.
AI may prove to be particularly advantageous in this context, as its precision allows for the detection of several crucial factors:
- an individual's liveness.
- identity forgery.
- fake, AI-generated images.
This ensures that the identity verification process is secure and reliable. And that's because AI technology is capable of detecting any fraudulent attempts to game the system. Additionally, it can make sure that the selfies provided during the verification process are authentic.
By using AI-Powered Proof of Individuality, ESelfKey may be able to provide a trustworthy and robust system for digital identity verification, which is critical in today's digital world.
The Benefits of ESelfKey iD Credential Locking
As stated above, digital identities have become a target for malicious players that seek to exploit others for personal gain. And, with the weak security in some centralized systems, it’s crucial that we look for alternatives.
Given this, ESelfKey's credential locking method may provide a robust, reliable, and decentralized method for identity verification. It may offer the level of security and privacy that is critical in today’s digital world. Individuals may benefit from peace of mind and ensure that their digital identities are protected from fraudulent activities.
Even more, unlawful access to one’s personal accounts may become very challenging due to the extra layer of protection added by AI. Simply providing a true, authentic selfie can achieve all of this.
Conclusions
The rise of data breaches and identity theft has highlighted the need for a trustless and secure environment for online interactions. Individuals need to have confidence in the systems they use to protect their personal information to ensure the security of their digital identities.
Unfortunately, centralized systems may fail to provide proper security measures, which often lead to data breaches involving identity theft.
With the use of ESelfKey iD Credential Locking, a much safer network may be available in the future. By locking their credentials, users may prevent identity theft and fraud. Not only that, but they may gain access to exclusive features and services within the ESelfKey ecosystem.
SelfKey's goal is to develop a secure and trustless environment for online interactions. And that is highly important nowadays, as we become more and more accustomed to operating in the digital world.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details. The term "staking" is used solely as it is described here and does not mean any investment or similar activities.
SELF and KEY tokens, SBTs, and NFTs associated with the ESelfKey ecosystem have no monetary value or utility outside of the ESelfKey ecosystem, are not ascribed any price or conversion ratio by ESelfKey and its affiliates, and do not represent ownership interests or confer any rights to profits or revenues. These tokens should not be purchased for speculative reasons or considered investments.
By engaging with ESelfKey, you acknowledge and agree to the applicable terms and any associated risks. We recommend consulting with legal and financial professionals before participating in the ESelfKey ecosystem and related transactions.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Have you ever seriously considered the negative impacts of a data breach? Are you aware of the digital safety risks that lurk around the corners of the internet? And, did you know that cyberattacks may produce life-long consequences?
Nowadays, applications and websites have become so common that we consider them an integral part of our daily lives. And, because we have normalized it, individuals blindly share their private information with little thought given to the implications of doing so.
We rarely ever stop to consider what happens to our personal data once we share it with large technology corporations. And that’s because we live with the illusion that our valuable or sensitive private information is safe. That cyber attacks cannot possibly reach us.
However, some serious privacy violations have occurred in the past several months. And they have exposed the severe effects of sharing personal information without proper caution to safety and privacy.
Despite data breaches occurring on a daily basis, they aren’t discussed as often as they should be. Individuals who have not experienced such incidents may assume that they are immune to them. But anyone can fall victim at any time, and the consequences of a data breach can be irreversibly harmful.
In this article, ESelfKey aims to provide an in-depth analysis of data breaches, recent events, and the potential aftermath for individuals whose personal information is compromised.
It is highly important to spread awareness about the possible consequences of data breaches. To attempt to prevent them from happening at all. With ESelfKey’s decentralized solutions, a safer digital future may await us.
Let us elaborate on these crucial aspects in the paragraphs below.
Highlights
- Defining data breaches: Meaning and Overview
- Factors contributing to data breaches: Why, Who, and for What?
- Caught Off Guard: When and Where Data Breaches Strike
- Victims of data breaches: Are you safe?
- Conclusions
Defining data breaches: Meaning and Overview
A brief, but fundamental introduction
Data breaches are serious security violations where confidential, protected or sensitive data is accessed, stolen or used by an unauthorized person or organization. These devastating incidents are also known as data spills, data leaks, or information disclosures, and they can occur in a variety of ways.
These digital attacks are typically well organized and initiated by malicious players, including organized crime, political activists, and national governments. However, even individuals who accidentally gain unauthorized access to systems with poor security configurations can cause data breaches.
The information that hackers may disclose can range from matters that may compromise national security to information that government officials want to keep hidden. When a person who has access to such information deliberately exposes it, for political reasons, it is usually referred to as a "leak".
The negative effects of a cyber attack: What happens after?
Data breaches can have far-reaching consequences, impacting a variety of information types including, but not limited to:
- financial data, such as credit card information and bank details.
- personally identifiable information (PII), such as full name, full address, IDs, birth certificate information, etc.
- personal health information (PHI), such as full name, home address, or dates related to the health or identity of individuals.
- trade secrets, and intellectual property.
- sensitive or valuable information, like photos or videos.
Unstructured data, such as files, documents, and private information, can also become exposed and vulnerable if proper security measures are not in place to protect them.
These cyberattacks aren’t limited to organizations or powerful institutions, though. Anyone could be a victim. And, worst of all, the compromise or theft of the information listed above can lead to anything from:
- financial losses
- identity theft
- reputational damage
- legal repercussions
It's important for individuals and organizations to take steps to protect their sensitive information and implement strong security measures to prevent data breaches.
ESelfKey understands the devastating consequences of data breaches and emphasizes the significance of implementing preventive measures. Responding promptly and adequately in case of such incidents is also highly important.
Recent Data Breaches: The beginning of 2023
The frequency of data breaches has increased in recent years. Alarmingly, the past several months have seen a handful of significant incidents.
- One such example is TikTok’s illegal processing of data belonging to 1.4 million children under 13, who were using its platform without parental consent. This breach highlights the importance of proper data management practices, particularly when dealing with children's information.
- Another example is the cyberattack on Yum! Brands, where attackers stole personal information belonging to some individuals, including names, driver's license numbers, and other ID card numbers. This kind of data is particularly sensitive and can be used to commit identity theft, among other crimes.
- Finally, the hacking of The Kodi Foundation resulted in the exposure of personal information and private conversations of over 400,000 users. Such incidents can have long-term consequences for the affected individuals, including reputational damage and financial losses. These breaches emphasize the need for better cybersecurity measures and data protection practices across industries.
Factors contributing to data breaches: Why, Who, and for What?
Cyberattacks have become a prevalent threat to our digital lives, and they occur on both personal and larger scales. While most people may assume that only organizations with weak security measures are at risk, individuals are also susceptible to data breaches.
In fact, personal cyberattacks often happen due to a lack of caution when it comes to protecting oneself online.
Why do data breaches occur?
One of the most common ways individuals make themselves vulnerable to cyberattacks is by using weak or predictable passwords. This makes it easy for hackers to access their accounts and steal sensitive information. Additionally, using the same password on multiple accounts makes it even easier for hackers to gain access to a person's entire online presence.
Lack of proper security measures is another way individuals put themselves at risk. Failing to have anti-malware protection on their devices can allow malware to infiltrate and infect their system. Similarly, exposing personal information publicly online, such as on social media, can provide hackers with the necessary information to carry out attacks.
Clicking on or accessing suspicious links is another way individuals can become victims of cyberattacks. It is worth mentioning that bad players often use phishing emails to trick people into giving up sensitive information. These emails can appear legitimate, so it's important to be cautious and verify the source before clicking on any links or providing personal information.
Who is responsible for data breaches?
Anyone could carry out a cyberattack, if they have the necessary tools, and if that is their intention.
Data breaches are a serious concern for individuals, organizations, and governments alike. These breaches are often the result of bad players with malicious intent. Perpetrators can range from organized crime groups seeking financial gain to political activists looking to disrupt or expose sensitive information.
In some instances, national governments have conducted data breaches for espionage or other motives. Regardless of the motive, it's important for individuals and organizations to take steps to protect themselves from potential breaches and to respond quickly and effectively if one occurs.
What are the intentions of those who initiate cyberattacks?
Malicious individuals typically have two main intentions: financial gain or causing damage to institutions for various reasons.
In pursuit of these goals, they may carry out data breaches that can have serious consequences for their victims. These attacks can result in the exposure of personal information and sensitive data, which can lead to identity theft, financial fraud, and other types of harm.
Sometimes, larger feuds between hackers and their targets can result in victims becoming collateral damage and suffering the consequences of attacks that were not specifically directed at them.
Caught Off Guard: When and Where Data Breaches Strike
Data breaches can happen every second and anywhere, from major technology companies to large financial institutions, and even in our own homes.
Public places such as cafes or airports, which offer public Wi-Fi, can also provide opportunities for hackers to access personal data.
Recently, incidents involving Yum!Brands and TikTok have highlighted the vulnerability of powerful institutions to cyber attacks. However, individuals are also at risk in their personal lives.
At any given moment, scam messages spread by viruses or hackers can target friends and family members. Weak personal security measures, such as predictable passwords and email addresses, can leave individuals vulnerable to attacks. As a result, the malware can spread to the victim’s circle of friends, family, or acquaintances via personal messages or emails.
One common method used by attackers is phishing emails. They appear to be legitimate messages from a trusted source but actually contain malicious links or attachments. Clicking on these links can result in the installation of malware on a device, allowing attackers to gain access to sensitive information.
Victims of data breaches: Are you safe?
Who do bad players target?
The victims of data breaches can be anyone whose personal data was involved, regardless of age, gender, occupation, or level of power.
This includes children, women, men, students, teachers, and employees who trust their employers with their personal information. It also includes clients, customers, and patients who share their data with businesses and healthcare providers.
It's important to recognize that anyone who uses the internet is at risk of being affected by a data breach, regardless of how small or popular they are. Constantly searching for vulnerabilities and ways to exploit them, bad actors can breach even the most seemingly secure systems.
That's why it's essential to take the right security measures, such as using strong passwords, regularly updating software, and being cautious when sharing personal information online. By being proactive about data security, individuals and organizations can help protect themselves and minimize the potential impact of a breach.
How can Data Breaches affect you?
Individuals can be affected by data breaches in two different ways:
- At a large scale, when a centralized system is hacked, which can affect millions of people.
- On a personal level, when an individual's personal online accounts are hacked. In this case, the breach may only affect one person, but it can still have severe consequences, such as financial loss or identity theft.
In both cases, it's crucial to take steps to protect yourself and your personal information. ESelfKey advises using strong passwords, enabling two-factor authentication, and regularly monitoring your financial accounts for suspicious activity.
Large Scale: Attacking Businesses
Large-scale data breaches can have far-reaching consequences that extend beyond the immediate victims.
While companies, institutions, and organizations are often the primary targets of such attacks, individuals can also suffer the consequences on a personal level. Even if the attack was not personally directed at them, they could still become collateral damage if the company they have trusted their PII with falls victim to a data breach.
The consequences of this kind of data breach can be severe and long-lasting, for instance:
- Companies can face financial losses, damage to their reputation, and even legal action.
- Institutions may lose the trust of their stakeholders and customers, leading to a decline in business.
- Organizations may find it difficult to attract and retain talent if they cannot demonstrate that they take data security seriously.
Furthermore, large-scale data breaches can lead to a loss of trust in the digital economy. If people cannot trust that their personal information is secure, they may be less likely to use online services and conduct transactions digitally. This could lead to a decline in e-commerce and other digital industries, negatively impacting the overall economy.
All in all, the consequences of large-scale data breaches are not limited to the immediate victims. Companies, institutions, organizations, and individuals can all suffer the effects of these attacks.
Below, we will examine some of these negative impacts more thoroughly.
Temporary Shut Down
Data breaches can have a significant impact on companies, not only in terms of the immediate costs but also in terms of long-term consequences. When a company experiences a data breach, it may be forced to halt its activity temporarily, which can result in millions of dollars in damages.
According to industry surveys, Gartner concludes that the cost of operational downtime can be around $5,600 per minute, which translates to $300,000 per hour. This can add up quickly, especially if the breach is not resolved promptly.
In addition to the financial costs, a data breach can also damage a company's reputation and erode the trust of its customers, leading to long-term consequences.
For example, Expeditors International is still dealing with the aftermath of a data breach that occurred in February 2022, which forced it to halt its activity temporarily. The company is likely to experience long-term consequences as a result, including a potential loss of business and damage to its reputation.
It is therefore crucial for companies to take proactive steps to prevent data breaches from occurring and to have a solid plan in place for responding to them if they do occur.
Financial Loss
Financial losses can arise from two main sources following a cyberattack:
- Ransomware
- Legal actions
Ransomware attacks can result in significant financial losses for organizations, as hackers can demand large sums of money in exchange for unlocking access to their encrypted data.
The growth of ransomware attacks is a cause for concern, with experts predicting that the total cost of ransomware damages worldwide could reach $265 billion by 2031.
Legal actions can also result in substantial financial losses for organizations. The Equifax data breach in 2017 affected over 145 million people worldwide and has already cost the company more than $700 million in compensation to affected US customers. The breach also affected an estimated 15 million customers in the UK, who have launched their own separate legal action in the high court seeking £100 million in compensation.
Legal actions can be costly and time-consuming, and the reputational damage caused by a data breach can have long-term consequences for an organization's financial performance.
Reputational Damage
Reputational damage is a major concern for companies that experience large-scale data breaches. Such damage can lead to revenue loss and have long-term impacts on the company.
When a company's reputation is tarnished due to a history of data breaches, people are less likely to trust the company with their payment information, and they may choose to take their business elsewhere.
This loss of trust can be difficult to overcome. Therefore, companies must take steps to protect themselves and their customers from data breaches. Additionally, they must try to maintain their reputation and ensure their long-term success.
Loss of Private Data
Sensitive data and intellectual property are two key areas that hackers target in a cyber attack.
Sensitive data can include, but are not limited to:
- Personal information belonging to customers, patients, and employees.
- Private company emails that contain personal health history, home addresses, and payment information.
When this type of data is breached, it can lead to significant financial losses and reputational damage for the company.
Intellectual property is another target of hackers, particularly designs, strategies, and blueprints. When intellectual property is stolen, the competition can take advantage of the leaked information. And this, in turn, may cause long-term damage to the company's competitive advantage.
Businesses within the manufacturing and construction industries are particularly vulnerable to these types of cyber threats. Therefore, many small businesses believe that they are unlikely to be targeted by hackers, but this is not the case.
In fact, 60% of all hacks target small businesses because they are often easier to attack. It is therefore crucial for businesses of all sizes to take proactive measures to protect their sensitive data and intellectual property from cyber threats.
Personal Level: Targeting the Individual
Data breaches at a personal level often occur due to a lack of caution when operating in the digital world and inadequate security measures.
People may accidentally share sensitive information, such as their social security number or credit card details, on unsecured websites. Alternatively, they could fall victim to phishing scams that trick them into revealing their login credentials.
Additionally, using weak passwords and not updating software and operating systems can leave personal devices vulnerable to hacking.
SelfKey’s decentralized solutions are centered around the individual’s privacy and security, with a strong emphasis on individuality. It is highly important for individuals to be vigilant when using digital platforms and take appropriate security measures to protect their personal data from cyber threats.
Identify Theft
Identity theft is a serious crime that can have devastating consequences for its victims.
When criminals gain access to a victim's personally identifiable information (PII), such as their full name, Social Security number, and birthday, they can wreak havoc on their financial and personal lives.
Victims can have their bank accounts emptied, credit histories ruined, and valuable possessions taken away. In some cases, victims have even been wrongly arrested for crimes they did not commit. This is because the criminal may use the victim's identity to commit cybercrimes or other illegal activities, leaving the victim facing legal action and potentially a criminal record.
Notable examples of identity theft
- The case of Nicole McCabe, an Australian woman suspected of murder after her passport was compromised and her identity stolen.
- Several victims of identity theft had to struggle with proving they were not responsible for the withdrawal of large amounts of cash from banks, or illegally attempting to obtain loans worth thousands.
- The terrifying story of Andorrie Sachs, whose medical identity was stolen by a pregnant woman who gave birth in Sachs' name and left the baby at the hospital, resulting in a $10,000 hospital bill.
Local authorities mistakenly reported Sachs as an unfit mother and threatened to take her children away. This could also have lifelong implications for Sachs as the perpetrator had a different blood type, and uncorrected medical records could result in Sachs' death if she ever needed a blood transfusion. A healthcare provider could even prohibit Sachs from reviewing her own medical records as they might not be in her name.
This is one of the many reasons why ESelfKey strongly encourages individuals to take proactive steps to protect their personal information, such as:
- Using strong passwords.
- Regularly checking their credit report.
- Being cautious when sharing personal information online.
By being vigilant and taking appropriate security measures, individuals can reduce their risk of falling victim to identity theft and the devastating consequences that can follow.
Personal Health Information
The theft of personal health information (PHI) is highly valuable on the Dark Web, as it can be worth more than 200 times stolen credit card information.
This type of identity theft can have serious consequences, including, but not limited to:
- Obtaining illegal medical treatments or prescription drugs.
- Altering the victim’s medical history.
- Using up the victim’s medical benefits.
Hackers can also sell stolen PHI to other criminals, who can use it for a range of illegal activities.
Given these horrifying facts, ESelfKey strongly advises individuals to take steps to protect their medical identity, such as:
- Regularly checking medical records for errors.
- Checking for signs of fraudulent activity.
- Ensuring that their healthcare providers have proper security measures in place to protect their PHI.
Financial loss
Once malicious individuals obtain your PII, they could potentially use it to damage your credit score and commit financial fraud.
A lowered credit score can make it challenging for the victim to:
- Obtain a personal loan.
- Secure a mortgage.
- Even impact job prospects.
Additionally, individuals who commit identity fraud can open new bank accounts in your name, drain your existing accounts, and commit check fraud. They can also apply for credit using your information, and engage in a variety of other banking scams. All things considered, it’s important to be vigilant in safeguarding your PII. The long-term financial consequences of a data breach can be severe.
Impersonation on Social Media
Cybercriminals can use your digital identity to carry out various malicious activities that can cause significant harm. Here are only a few terrifying examples:
- They can use your digital identity to phish for credentials from your friends and family, leading to further attacks.
- They can ruin your reputation by posting obscene or profane content online, damaging your personal and professional relationships.
- They may look for sensitive photos and videos in your account and use them to extort you, leading to emotional distress and financial loss.
As horrifying as this may sound, there are ways to prevent this kind of disaster from causing irreparable damage to your digital identity. For instance, ESelfKey’s AI-Powered Proof of Individuality methods may be the key to protect individuals against identity theft.
Emotional and Mental impact
A personal data breach can lead to significant mental and emotional distress. The harm caused can take a long time to recover from, depending on the extent of the damage done by the hacker.
Along with reputational damage, victims may also have to spend a considerable amount of time and money to mitigate the fallout. And, the steps towards recovering from such a cyberattack could be draining in themselves.
Victims may have to spend endless hours or days:
- Contacting their bank, lenders, and creditors.
- Securing all their online accounts.
- Replacing stolen identification documents.
- Canceling and replacing bank accounts and credit cards.
- Dealing with criminal charges made in their name.
Victims will also need to remove malware and viruses from their devices, while constantly proving their identity and showing that it was stolen. A process which can be emotionally, mentally, and physically exhausting in itself.
Worst of all, if affected individuals fail to repair compromised information or remove malware from their devices, they will risk falling victim to the same attacks over and over again.
The long-lasting consequences of a data breach can be devastating, particularly if your PII or PHI end up on the Dark Web. The information could be in circulation there indefinitely, making you vulnerable to further harm.
SelfKey’s visions for a safer digital future
Recent events have demonstrated the devastating impact that data breaches can have on individuals and organizations. That's why ESelfKey is emphasizing the importance of security when it comes to online interactions and digital identities.
By developing decentralized solutions with Self Sovereign Identity in mind, ESelfKey is using the potential of modern technology in its aim to counteract these breaches. AI-powered proof of individuality is one solution that may fight against maliciously used AI, to prevent identity theft.
It's important to raise awareness about data breaches and their potential consequences. To teach individuals and organizations about how to prevent them or how to respond in case one occurs.
Conclusions
In this modern, digital world, we have normalized sharing our personal data online. However, this does not mean that our personal information is necessarily safe.
In fact, data breaches are becoming more and more common, and the consequences can be severe and irreversible. That's why it's crucial for individuals and organizations to take caution when sharing and storing their personal data.
ESelfKey is focused on developing solutions which may prevent data breaches and enable individuals to operate safely in the digital world. At the heart of their approach is a commitment to the idea that privacy is a basic human right that should not be traded for convenience.
By prioritizing privacy and security in their technology solutions, ESelfKey is aiming to help empower individuals to take control of their digital identities and protect their personal information.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>Maintaining the privacy of our personal data is crucial for our safety and the safety of our loved ones as we navigate the online world. However, the question arises: how anonymous can we be before losing our sense of “self” in the sea of faceless identities?
ESelfKey introduces a possible solution with Customizable Non-Fungible Tokens (NTFs), called Normies.
ESelfKey iD may be the best approach to managing digital identities with the data owner at the helm. And, by attaching Normies to a ESelfKey iD, individuals may be able to build the outer layer of their online identity. With a wide variety of digital assets that can be combined in countless ways, Normies can be designed directly by the user, so that they will fit the user’s personal preference or needs.
This way, individuals may continue to express their personality and creativity online, while keeping the security of their valuable, private information.
In this article, we will thoroughly explore the possibilities SelfKey’s NFT packs offer, as well as how to obtain and mint them.
Highlights
- ESelfKey iD and NFTs
- SelfKey’s Customizable NFTs
- NFT packs and How to Obtain Them
- NFTs and Web3
- Conclusions
ESelfKey iD and NFTs
A brief introduction of ESelfKey iD
ESelfKey iD is an innovative approach to online identity verification which may be a better solution than traditional KYC (know your customer) checks. It emphasizes digital security and privacy, so that individuals may safely navigate the online world.
One of the key benefits of ESelfKey iD is its ease of use and affordability, which may make it more accessible to users. The overall process is streamlined and easier, removing the need for complex and time-consuming traditional KYC checks. This may not only save time for users but also reduce costs associated with the verification process.
Additionally, the onboarding process with ESelfKey iD is quick and efficient, which may enable users to establish their online identity swiftly.
Furthermore, ESelfKey iD eliminates the need for repeated collection and storage of personally identifiable information (PII). Existing KYC checks are reused, which may lower the risk of PII display and reduce the potential for identity theft. This may enhance the overall security and privacy of users' personal information, which is crucial in today's data-driven world.
All in all, ESelfKey iD may provide a more accessible, efficient, and secure solution for establishing online identity while enhancing user privacy.
ESelfKey iD and NFTs
The ability to customize one's digital identity can be a powerful tool for self-expression. Individuals may be able to showcase their personality, creativity, and style in the online world.
To increase user-friendliness, ESelfKey introduces a unique feature that allows users to attach a distinct NFT series to their ESelfKey iD profile picture. This innovative component may not only add a touch of personalization and originality to the user's digital identity but it also reflects the growing trend of NFTs in the crypto space.
By embracing the boundless possibilities of this new element, individuals may have the opportunity to develop a digital avatar that perfectly aligns with their unique preferences and interests.
This customization aspect may empower users to truly own and personalize their digital presence. Such an element may result in a sense of ownership and confidence in their virtual identity. Furthermore, it may lead to a more immersive and enjoyable user experience. Members can express themselves in a way that reflects their individuality while increasing their privacy.
The addition of the NFT series feature to the ESelfKey iD platform is a testament to ESelfKey's commitment to user-friendliness, personalization, and innovation.
SelfKey’s Customizable NTFs
The Normies Project
The Normies Project aims to offer individuals an unparalleled experience in the world of digital assets. It consists of two well defined NFT collections, each with its own unique features and offerings:
- Base NFTs
- Wearables
What are Base NFTs?
Base NFTs are equipable avatars that can be personalized with wearables to dress up one’s Normies. With Base NFTs, all verified users may have the power to mint their own avatar. As there is no maximum supply, Base NFTs allow for limitless creativity and customization.
As an added bonus, every ESelfKey iD owner will receive one free Base NFT, making it accessible to all.
Users may express their individuality by customizing their own avatar with a wide range of wearables. Furthermore, they may use their Normies in virtual spaces, social gatherings, and gaming adventures.
How to obtain a Base NTF Avatar
Obtaining a Base NTF Avatar may be an exciting step towards personalizing your virtual identity in the metaverse.
The process is rather simple:
- To begin, you'll need to go through a simple verification process.
- Once you're verified, you'll gain access to the standard customizations available for your Base NFT Avatar. This may allow you to create a unique digital representation of yourself.
- After customizing your Base NFT Avatar, you can mint it for free, making it officially yours in the virtual world.
- With your Base NFT in hand, you have the option to further enhance your avatar by purchasing wearable packs. Community members may sell these packs, along with individual NFTs, on OpenSea and other popular NFT marketplaces.
These wearables and NFTs may help you express your personality, interests, and style within the metaverse. Likewise, they may add a layer of originality and individuality to your digital presence.
What are wearables?
Wearables are an exciting addition to the world of NFTs, offering users the ability to further customize and personalize their Base NFT avatars.
From hairstyles to shirts, hats, and beyond, wearables come in various categories, allowing users to express their individuality and style in the metaverse. By adding wearables to their Base NFTs, users can increase the rarity of their NFTs, making them even more unique.
Obtaining wearables is typically done through NFT packs. These packs may contain a wide selection of digital items that users can add to their avatars. The packs may also allow users to acquire new wearables to enhance their Base NFT avatars. This way, users may feel a thrilling experience of discovery.
With wearables, users have the power to transform their digital personas into something truly one-of-a-kind. This gives users a good opportunity to showcase their creativity and personality in the metaverse. All in all, wearables are a key tool in personalizing Base NFT avatars to make them truly original and special. Customization includes, but is not limited to: trendy hairstyles, stylish shirts, or fashionable hats. All of which may make your NFT reflect your uniqueness.
NFT Packs and How to Obtain Them
Purchasing NFT packs
Users have the option to purchase NFT packs, which contain a curated selection of wearables to customize their Base NFT avatars.
Depending on the chosen pack, users may reveal up to 10 different wearables, from hairstyles to shirts, hats, and more. The number of packs users can buy have no limits, which may offer members endless chances to design their NFTs.
Users can buy NFT packs, or redeem NFT packs using SELF tokens, minted by performing tasks that benefit ESelfKey DAO. This unique approach allows users to actively participate in the community. Active participants may mint tokens that can be used to obtain NFT packs and further customize their Base NFT avatars.
Alchemy
Members have the option to use their duplicate wearables for a chance to generate super rare wearables, adding an exciting element of rarity and exclusivity to the customization process. By utilizing duplicates, users can participate in a special feature that regulates the number of wearables in existence. This element may make them even more original.
This feature adds an element of gamification to the NFT experience, allowing users to engage in strategic decision-making to potentially unlock unique and highly coveted wearables.
Such an innovative approach may encourage users to actively manage their collection. Simultaneously, it contribute to the rarity and scarcity of certain wearables, making them highly desirable among collectors.
It may be an exciting way for users to participate in the evolution of their NFT ecosystem and potentially obtain one-of-a-kind, super rare wearables to further customize their Base NFT avatars.
Expansion Packs
With changing seasons, exclusive and time-limited collectible NFTs may be introduced into the packs. These limited-edition NFTs offer a unique opportunity for users to acquire rare and highly sought-after digital assets that are only available for a limited time.
With each new period or season, the NFT packs may be updated with a fresh batch of exclusive collectibles. This may add excitement and anticipation to the design process. These limited-edition NFTs may feature special designs, themes, or functionalities that are only available for a specific timeframe. This method may create a sense of urgency and exclusivity among collectors.
Users who are eager to expand their collection and obtain unique NFTs may be motivated to keep an eye out for these periodic updates and seize the opportunity to acquire these exclusive assets before they are no longer available.
This dynamic and ever-changing aspect of the NFT ecosystem adds a layer of excitement and rarity to the customization experience, allowing users to continually enhance and evolve their Base NFT avatars with new and exclusive collectible NFTs.
NTFs and Web3
In the future, Normies may play a significant role in Web3 games, granting access to exclusive areas within the games and providing bonuses to the play-to-earn rewards.
These digital assets will serve as keys to unlock special traits, areas, or uses that are otherwise out of reach to regular players. By owning specific NFTs, players may gain entry to exclusive areas of the game world, revealing hidden treasures, unique challenges, or rare resources and bonuses.
This integration of NFTs in Web3 games may add a new side of ownership and utility to these digital assets. Furthermore, it may allow players to not only design their Base NFT avatars. At the same time, it may also enhance their gameplay and overall experience.
It creates a favorable relationship between NFT holding and in-game achievements. This may incentivize players to collect and utilize these digital assets to gain an edge in the virtual world.
Conclusions
ESelfKey iD may offer a diverse range of assets that can be utilized for customization, allowing us to express ourselves freely in the online world while striving to safeguard our private information from prying eyes.
With ESelfKey iD, we may confidently navigate both Web2 and Web3 spaces, knowing that our data may remain under our personal control and ownership. However, we can still make ourselves stand out and be recognized by our unique and one-of-a-kind NFTs.
By utilizing ESelfKey iD, we may strike a balance between privacy and self-expression, creating a personalized online presence while increasing control over our sensitive information. Overall, it may be an ideal way to operate in the digital world with confidence and freedom.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF tokens have no monetary value and are not ascribed any price or conversion ratio by ESelfKey and its affiliates. Additionally, SELF tokens do not confer any right to participate in any profits or revenues or represent any ownership interest. SELF tokens may have value and utility solely within ESelfKey.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details.
]]>
As the world continues to advance technologically, we find ourselves more and more immersed in the digital realm. Our digital identities have become just as important as our physical ones, and with this comes the need for secure and reliable online authentication systems.
However, traditional identity verification methods are becoming increasingly vulnerable to hacking and data breaches. This leads to a growing need for decentralized and more secure alternatives to centralized systems.
SelfKey focuses on providing safer and more reliable identity verification solutions. These options may be easier and more cost-effective than traditional KYC (Know Your Customer) methods.
In this article, we will explore how ESelfKey iD works, as well as its innovative features and benefits. We will elaborate on how it differs from traditional identity verification systems and why it may be a better option for individuals in the digital age.
Highlights
- What is a ESelfKey iD?
- How does ESelfKey iD work?
- Minting SBT
- Access to ESelfKey DAO
- Conclusions
What is a ESelfKey iD?
A brief introduction
ESelfKey iD is a cutting-edge technology that may revolutionize the way we verify our identities online. With its innovative on-chain credential system, ESelfKey iD may offer a faster, more secure, and less costly alternative to traditional KYC methods.
This new approach to online identity verification is the result of extensive research, user feedback, and collaboration. ESelfKey shares the vision of industry experts such as W3C and the authors of the soulbound token paper to potentially create a modern and reliable identity verification solution.
With ESelfKey iD, users may have complete control over their digital identities. They may manage their credentials, store them securely and share them only with the parties they choose. This may not only give users greater peace of mind but it might also help prevent identity theft and fraud.
Overall, it may be a significant step forward in the evolution of identity verification. And, it may have the potential to transform the way we authenticate ourselves online.
Why ESelfKey iD?
ESelfKey iD has a clear purpose - to provide companies with a streamlined and efficient KYC process that may improve compliance, reduce costs, and enhance customer privacy.
By leveraging blockchain technology, ESelfKey iD may offer a more secure and efficient way for companies to verify the identities of their customers.
This may not only lead to a better experience for customers but it may also aid companies in increasing their profitability. With ESelfKey iD, companies may enjoy a more efficient and secure system, while customers may enjoy a smoother and more hassle-free onboarding experience.
Ultimately, ESelfKey iD may be a win-win for everyone involved.
Ease of Use
For identity owners or data subjects, the ease of use when it comes to digital identity schemes primarily depends on how easy it is to enroll and use their credentials.
ESelfKey iD is designed with simplicity in mind, utilizing soulbound tokens so that users may easily produce their credentials using any non-custodial wallet.
With ESelfKey iD, the enrollment process may be as easy as a one-click option for users, with the heavy lifting happening behind the scenes.
All in all, ESelfKey iD may offer a user-friendly approach to digital identity schemes that may make it easy for users to produce, maintain, and use their credentials. At the same time, it might also provide a secure and decentralized solution that meets the needs of the modern digital age.
ESelfKey iD vs traditional KYC checks
ESelfKey iD may be a better alternative for identity verification, as it may offer a more efficient, secure, and user-friendly approach to KYC.
By using the potential of blockchain technology and smart contracts, ESelfKey iD may provide a secure, decentralized, and efficient identity verification process. It may have the potential to eliminate many of the issues associated with traditional KYC methods, possibly making the process more user-friendly and safe.
Not only that, but with ESelfKey iD, users may have complete control over their digital identities and they might exercise their SSID rights more easily than ever before.
How does ESelfKey iD work?
Obtaining a ESelfKey iD is a smooth and hassle-free process that prioritizes user convenience without compromising security and privacy. The streamlined procedure may ensure that users have access to a secure and private digital identity that they can trust.
The process
By following the simple steps outlined by the platform, users can obtain a ESelfKey iD quickly and with ease. The steps are as follows:
1. Users must first log in with their wallet and pay an entry fee.
2. The next step would be to undergo a KYC verification process. This method is designed to ensure that the user's identity is authentic and that they meet the necessary eligibility criteria.
The verification process typically consists of:
- performing a selfie check.
- providing personal information, such as name and address.
- providing government-issued identification documents, such as a passport.
Additionally, users will not be able to create duplicate accounts.
3. Once the KYC process is complete, legible users are automatically approved.
4. The final step in the process is to mint the soul-bound ESelfKey ID NFT. This unique digital asset is generated using blockchain technology and is securely bound to the user's digital identity.
It might serve as proof of identity (POI) and it may be used to authenticate the user's identity in a variety of settings, such as:
- online marketplaces.
- financial institutions.
- other digital platforms, such as social media and videogames.
Even more, as the concept of the metaverse gains popularity, the need for secure and reliable digital identities becomes increasingly important. ESelfKey iD emphasizes privacy and self-sovereignty. Therefore, it may be the perfect identity credential for the exciting products and services of the future.
Minting soul-bound ESelfKey ID NFT
Aggregating Multiple Credentials
By combining different SBT (soul-bound tokens) and identity credentials, ESelfKey iD may provide a higher level of verification for the user's identity.
Credentials which may be aggregated by a ESelfKey iD include, but are not limited to:
- Metaproof.
- KYC credentials issued by ESelfKey Network issuers.
- Traditional accounts, such as: Google, Apple, Discord, Github, Twitter, and the likes.
- Various identity tokens, such as Binance’s BAB token issued in 2022.
This implementation may have significant advantages over individual credentials, as it may increase the reliability and accuracy of identity verification. And, an increase in reliability and accuracy is crucial for online interactions and services that require trust between parties.
The more credentials added to the ESelfKey iD container, the more trust may be established, and the more reliable and secure the user's digital identity may become.
Furthermore, the integration of multiple SBTs and identity credentials within a ESelfKey iD container might provide users with unparalleled flexibility. This may enable them to add as many credentials as they require to establish their identity in a variety of contexts.
This feature may enhance the ESelfKey platform's versatility and utility. It might make it more appealing to individuals and institutions seeking a reliable and secure digital identity solution.
Essentially, ESelfKey's implementation of an aggregated credential system in its platform may be a significant step forward in the development of a strong and reliable self-sovereign identity ecosystem.
Attaching NFT series to ESelfKey iD
ESelfKey continues to prioritize user-friendliness with the introduction of a unique feature that may enable users to attach a distinct NFT series to their ESelfKey iD profile picture. This feature may add a touch of personalization and uniqueness to the user's digital identity. Even more, it might reflect the growing trend of NFTs in the crypto space.
Additionally, it may also enhance the user's experience by providing them with more options to personalize and showcase their digital identity.
Ultimately, the addition of the NFT series feature to the ESelfKey iD platform reflects the platform's continued focus on user-friendliness, personalization, and innovation.
Access to ESelfKey DAO
Obtaining a ESelfKey iD may provide users with numerous benefits that enhance their experience on the platform and beyond.
These benefits may include:
- access to the governance of the ESelfKey Protocol.
- the ability to mint SELF tokens.
- participating in locking a POI credential.
- exclusive access to member-only channels on Discord.
- obtaining exclusive collectible NFT packs.
- registering for KEY.ETH ENS domains.
- enjoying instant login to partner apps.
Minting SELF tokens
Having access to the ESelfKey DAO may enable users to mint their own SELF tokens. The token might then be used for various purposes and services on the ESelfKey platform.
This feature may add value to the user's experience and may provide them with more control over their digital identity.
Locking
By locking KEY tokens on their KYC credential, users may mint SELF tokens. Locking credentials may be a way for individuals to demonstrate confidence in the accuracy of their data. This, in turn, may increase the validity of their credentials. Users may withdraw tokens at any time, although this will result in the termination of SELF token generation.
Exclusive Discord Channels
Access to member-only Discord channels may be another perk of having a ESelfKey iD. It may provide users with a community to engage with other DAO members through a designated channel. DAO members may also discuss proposals for the governance of the DAO.
NTF packs
Exclusive collectible NFT packs may also be available to ESelfKey iD holders. This may add a unique and personalized touch to their digital identity. These collectibles are released by the ESelfKey DAO, further enhancing their customization and originality.
KEY.ETH ENS domains and ESelfKey iD
Moreover, ESelfKey iD holders may register for KEY.ETH ENS domains. This might enable them to create unique and easily identifiable domains for their online identity.
Instant login to partner apps
Instant login to partner apps may be another advantage of having a ESelfKey iD. This may provide users with a seamless and secure login process across multiple platforms.
Ultimately, the benefits of having a ESelfKey iD express the platform's commitment to providing users with a comprehensive, valuable experience. It may enhance their ability to navigate the crypto space with ease and confidence.
Conclusions
In theory, ESelfKey iD may be a strong and reliable form of digital identity that might be used for a broad range of use cases in the crypto world. With its focus on user-friendliness, security, and privacy, the ESelfKey iD may be well-suited to the needs of decentralized societies and Web3 applications.
However, ESelfKey iD may also be suited for traditional Web2 platforms that want to benefit from security and anti-bot features inherent to the ESelfKey iD system.
ESelfKey iD may not only empower the governance of the ESelfKey DAO but it may also provide a model for other decentralized governance systems. By offering powerful, privacy-preserving identity credentials, the ESelfKey iD might enable more fair and democratic governance. This way, users may have greater control over their data and identities.
The ESelfKey DAO aims to provide new forms of decentralized governance, which may allow members to experiment with different approaches and explore the full potential of the ESelfKey iD.
As the crypto world continues to evolve, the ESelfKey iD might play an increasingly important role in enabling secure and transparent transactions across a wide range of platforms and applications.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. We do not solicit or offer to buy or sell any financial instrument.
SELF tokens have no monetary value and are not ascribed any price or conversion ratio by ESelfKey and its affiliates. Additionally, SELF tokens do not confer any right to participate in any profits or revenues or represent any ownership interest. SELF tokens may have value and utility solely within ESelfKey.
The purchase of a KEY token is not an investment. KEY tokens should not be bought for speculative reasons. A KEY token does not give any right to profits, and it does not represent any ownership interest. KEY tokens may have value and utility solely within ESelfKey.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details.
]]>Nowadays, most individuals operate in a digital environment where transactions and communication are made online. As a result, digital identity verification has become a very important aspect of online security and compliance.
KYC (Know Your Customer) is one of the most widely used methods for verifying the identities of users and clients. While KYC has been effective in assuring security and regulatory compliance, it has some significant drawbacks. KYC can be time-consuming, expensive, and difficult for users, potentially resulting in losing customers and missing business opportunities.
ESelfKey addresses this issue by proposing a potential solution to these issues with ESelfKey iD.
ESelfKey iD is a revolutionary approach to identity verification that could be faster, more secure, and less costly than traditional KYC methods. It uses the power of blockchain technology and smart contracts to potentially offer a secure, decentralized, and efficient identity verification process. This can possibly eliminate many of the issues associated with traditional KYC methods.
With ESelfKey iD, users can create a self sovereign identity that they can control, giving them more privacy and full ownership over their personal data.
In this article, we will elaborate on the drawbacks of traditional KYC methods. We will also examine the advantages of ESelfKey iD, its features and benefits compared to traditional KYC. Additionally, we will explore the potential impact of ESelfKey iD on the future of digital identity verification.
Highlights
- KYC: Potential Issues to Consider
- The Benefits of ESelfKey iD
- High-Level Flow
- Quick Relying Party Onboarding
- The Issuance: ESelfKey iD NFT User Flow
- The Verification: ESelfKey iD User Onboarding
- Reusable KYC and ESelfKey iD
- ESelfKey iD New Project Setup
- Conclusions
KYC: Potential Issues to Consider
Even though KYC has become a commonly used procedure in many industries, it has its drawbacks.
Here as some examples:
- The collection of personally identifiable information (PII) for KYC purposes comes with legal responsibilities and storage costs, which can take a toll on companies.
- Users have a tendency to dislike KYC checks, finding them intrusive and time-consuming. This can lead to lower conversion rates and a negative first impression for potential customers.
- Implementing KYC can be a difficult and expensive process, further adding to its disadvantages.
Perhaps the time to explore alternative ways of verifying customer identities has come. With ESelfKey iD, you can explore methods that are less tedious for all parties involved.
The Benefits of ESelfKey iD
As stated above, KYC processes can be inconvenient for both companies and customers alike. However, ESelfKey’s Ai-Powered Proof of Individuality method along with ESelfKey iD can potentially become a better alternative to KYC.
Here are some of ESelfKey.iD’s benefits:
- The overall process is easier and less costly, making it more accessible for users.
- The onboarding process is quick.
- Ongoing monitoring makes sure that customer data remains accurate.
- Existing KYC checks are reused, thus the need to collect and store PII repeatedly is no longer an issue.
- Costs for companies are reduced, but also improves customer privacy and security.
- It provides powerful compliance tools, ensuring that companies remain in compliance with regulations and laws.
By using ESelfKey iD, companies can streamline their KYC processes, reducing costs, enhancing customer privacy, and improving compliance. Ultimately, this results in a better experience for customers and a more efficient and secure system for companies.
Below, we will discuss some of ESelfKey iDs benefits more in depth.
High-Level Flow
ESelfKey iD enables zero-knowledge interactions between individuals, making sure that users' data is kept private and secure. With ESelfKey iD, the user's data does not reach your server. This adds to user privacy and prevents potential data breaches.
Furthermore, the onboarding process is quick and simple.
When a user with a ESelfKey iD visits your server, they are checked to determine if they match your filter. If they do, they can be onboarded instantly, simplifying the process and reducing the time and resources required.
By using ESelfKey iD, companies can provide a secure and efficient onboarding process that prioritizes user privacy and security. The zero-knowledge interactions and instant onboarding features make it a better alternative to traditional KYC processes.
Quick Relying Party Onboarding
To streamline the onboarding process, the following steps are required:
- Sign up at ESelfKey iD to create your user filters.
- Add these filters to your smart contracts.
- When a user attempts to run your smart contract function, the system will check if they have a ESelfKey iD NFT. If they do not have one, they will be prompted to get one.
- If the issuer has a ESelfKey iD NFT, they will then be able to verify whether the user matches the filter that you have set for the transaction. If they do, the user will be granted access to your server. If not, the user will be denied access.
Following these steps, companies can implement a more efficient and secure onboarding process that prioritizes user privacy and security.
ESelfKey iD's NFT-based system ensures that only authorized users are given access to the company's services. This reduces the risk of relying parties allowing access to unauthorized individuals to their services.
The Issuance: ESelfKey iD NFT User Flow
The issuance process for ESelfKey iD is outlined below:
- The user visits your project and is redirected to ESelfKey iD, in case they do not already have one.
- The user pays for the verification check.
- The user goes through the verification process, and the issuer stores their data. Ongoing monitoring of the account begins.
- If the user passes the checks, the issuer releases a credential that verifies the user's humanity, uniqueness in the database, and verified data.
- The user then mints their own ESelfKey iD NFT.
By following these steps, users can obtain a ESelfKey iD NFT that verifies their identity and potentially provides access to various projects that use the ESelfKey iD platform.
The verification process may grant access only to authorized users, providing enhanced security and privacy for both users and companies.
Enhanced security offers several benefits such as:
- Anti-bot security. This measure prevents automated attacks by detecting and blocking suspicious or malicious bot traffic.
- Fraud protection. Malicious individuals often use bots for fraudulent activities like creating fake accounts or generating false clicks to generate revenue. Implementing anti-bot security measures helps to identify and prevent such fraudulent activities, keeping the business and customers safe.
- Improved user experience. Bots can significantly hinder the user experience by slowing down websites or making it difficult for users to access information. Anti-bot security measures ensure that legitimate users can access the website or service without interruptions or delays.
The Verification: ESelfKey iD User Onboarding
The onboarding process for ESelfKey.iD is as follows:
- A user with a ESelfKey iD visits your project.
- You request that the ESelfKey iD issuer checks the user's information.
- The issuer verifies whether the user's data matches your filters.
- The issuer sends a signed message confirming the user's status.
- If the user is verified, they can be onboarded, and the signed message can be used to authorize transactions.
- The relying party (issuer) is billed for the verification check.
Through this process, companies can implement a more efficient and secure onboarding method that prioritizes user privacy and security.
ESelfKey iD's NFT-based system may allow access to the company's services only to authorized users. The use of a signed message adds an extra layer of security, offering further assurance that the user's data has been verified by the relying party.
Reusable KYC and ESelfKey iD
The benefits of using reusable KYC with ESelfKey iD are as follows:
- Your project subscribes to ESelfKey iD.
- Your project can be featured on the ESelfKey iD website.
- A user with a ESelfKey iD NFT visits the ESelfKey iD website.
- The user scrolls through the list of projects that support ESelfKey iD.
- The user can potentially choose your project from the list.
- The user quickly onboards to your project using their existing ESelfKey iD NFT.
- Your project profits from the seamless onboarding experience.
ESelfKey iD's reusable KYC system could provide companies with a more streamlined onboarding experience for users. Users can easily access multiple projects without having to go through the time-consuming and costly process of verifying their identity each time.
Additionally, companies benefit from increased user adoption and loyalty, as the reusable KYC system encourages users to choose projects that support ESelfKey iD. Overall, this system offers a win-win situation for both companies and users alike.
ESelfKey iD New Project Setup
Setting up a new project with ESelfKey iD is quite easy. Below, we will detail a few steps which you need to consider.
The project onboarding process is as follows:
- Go to the ESelfKey iD website.
- Register for a new account.
- Add your company privacy policy to your account.
- Choose a subscription pack that suits your needs.
- Set up filters to verify your users' identity.
- Your project is now ready to implement the filters into your system.
ESelfKey iD's easy-to-use platform could offer companies a quick and efficient way to set up their project's identity verification process. The platform provides a range of subscription plans to choose from, depending on your business's specific requirements.
With the ability to customize filters for your users, you can ensure that only authorized individuals can access your platform, enhancing security and trust.
Overall, ESelfKey iD's new project setup process offers a simple and effective solution for individuals looking to integrate identity verification into their systems
The Library Implementation
To implement ESelfKey iD into your project's system, follow these simple steps:
- Implement the backend library onto your server.
- Prepare the front-end to handle calls for authorization.
- Implement the ESelfKey iD smart contract into your own smart contract.
- Your project is now ready to onboard users.
By following these steps, you can integrate ESelfKey iD into your project's system and take advantage of its powerful identity verification capabilities. With the backend library in place, your server will be able to communicate with ESelfKey iD to authorize user access.
By integrating the smart contract into your own contract, you can ensure that only authorized individuals can access your platform, boosting security and trust.
All in all, ESelfKey iD's library implementation process offers a robust solution for businesses looking to enhance their identity verification capabilities.
How the Profile Builder Functions:
ESelfKey iD's Profile Builder is a tool that allows you to create customizable filters for your project. You may use these filters to sort and manage users based on specific criteria.
The Profile Builder allows you to create multiple filters, which you can implement separately on your project. This means that you can have different filters applied to different sections of your app or website, depending on your specific needs.
For example:
- You could create a filter that accepts citizens of Country A for one section of your app, but another filter for the same project that excludes citizens of Country A from another section.
- This level of detailed filtering allows you to match regulatory requirements while also boosting the benefits of your app.
To set up the Profile Builder, you would first define the standards you want to filter by, such as citizenship, age, or profession. You can then apply rules and conditions to each filter to create a customized sorting system.
For the most part, the Profile Builder in ESelfKey iD could provide a flexible and powerful tool for managing user data and creating a tailored experience for your app's users.
Conclusions
ESelfKey aims to provide a comprehensive solution that addresses the needs of both businesses and users.
The benefits of ESelfKey iD could include efficient, secure, and cost-effective KYC checks, streamlined onboarding, and better conversion rates. Additionally, ESelfKey iD's approach to privacy ensures legal compliance and reduces costs associated with PII storage.
Even more, with a user-friendly one-time KYC process and access to multiple projects on the website, ESelfKey iD offers convenience and ease of use for users. ESelfKey iD's project features and powerful user filtering tools could enable businesses to match rules and increase profitability.
Stay up to date with ESelfKey on Discord, Telegram, and Subscribe to the official ESelfKey Newsletter to receive new information!
Note:
We believe the information is correct as of the date stated, but we cannot guarantee its accuracy or completeness. We reserve the right not to update or modify it in the future. Please verify all information independently.
This communication is for informational purposes only. It is not legal or investment advice or service. We do not intend to offer, solicit, or recommend investment advisory services or buy, sell, or hold digital assets. Additionally, we do not solicit or offer to buy or sell any financial instrument.
We use the "KYC" term here for general information purposes, without reference to particular legislation. Please check the laws relevant to you and contact us for the details.
This document may contain statements regarding future events based on current expectations. However, some risks and uncertainties could cause results to differ. The views expressed here were based on the information that may change if new information becomes available.
]]>